How to manually block IPv6 on Linux
- Reading
- 2 mins
- Category
- Troubleshooting
The official Proton VPN Linux app now supports IPv6 connections.
Learn more about Proton VPN and IPv6 support
We recommend using our official Proton VPN app on Linux. However, it is also possible to manually configure a VPN connection in Linux using the WireGuard® or OpenVPN VPN protocols.
If using a manual VPN connection, we recommend disabling IPv6 to ensure no leaks can occur. The following solution should work for most Debian-based distros.
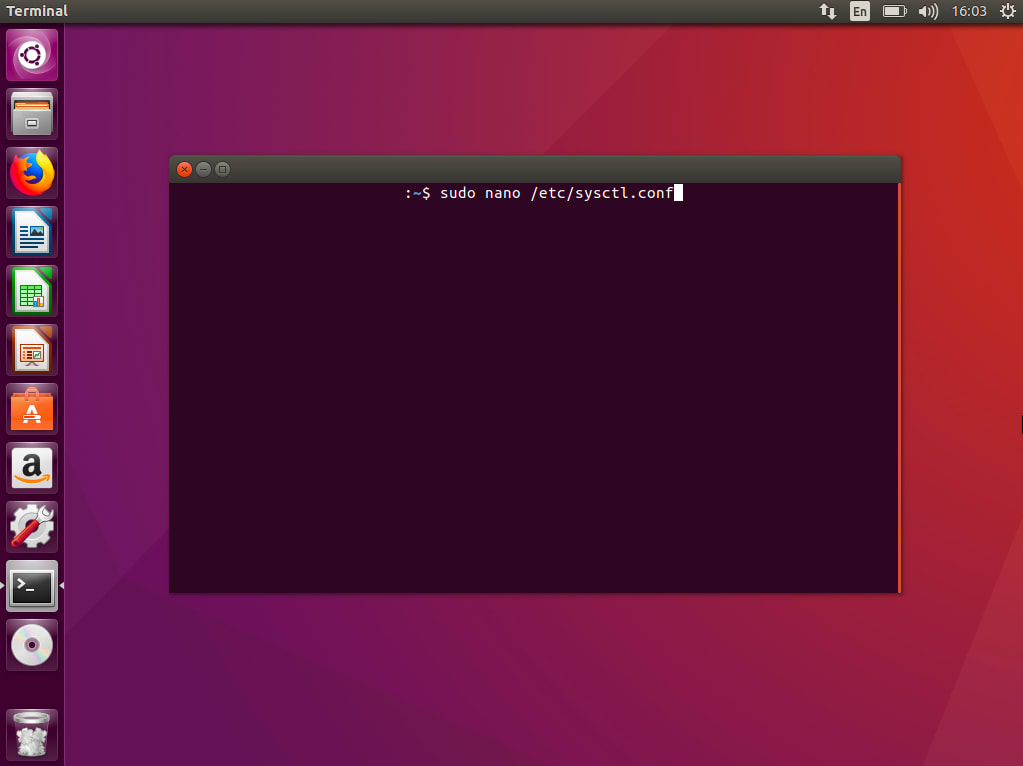
1) Open Terminal and enter the command:
sudo nano /etc/sysctl.conf
2) Add all the lines to the bottom of the file and save it:
net.ipv6.conf.all.disable_ipv6 = 1

3) Now make the system read the file and confirm the changes using this line:
sudo sysctl -p
That’s it! To check whether IPv6 was disabled on your computer, you can do an IPv6 leak test here(new window).
Related articles:
How to use Proton VPN on Linux
How to disable IPv6 on Windows
How to disable IPv6 on macOS