Protecting Proton VPN’s infrastructure
We protect your data with only the strongest encryption. We also go to great lengths to protect Proton VPN’s physical infrastructure.
- We own, ship, and install our Secure Core servers ourselves.
- Our servers are housed in secure data centers with biometric security.
- All VPN servers have full-disk encryption to secure their server certificates.
Multiple layers of VPN security
Your security is our primary concern, which is why we consider and address every potential vulnerability in our VPN service. To keep your data as secure as possible, we house our critical infrastructure in highly secure locations and limit access to our VPN servers to approved partners.
Secure locations
Our critical infrastructure, like our Secure Core VPN servers, is housed in secure data centers or on former military bases. Using these locations prevents anyone from being able to tamper with our servers.
Limited access
We installed all our Secure Core infrastructure and operate it ourselves to prevent anyone from gaining unauthorized access to our servers. These extra security precautions prevent our hardware from being compromised or tampered with.
Full-disk encryption
Full-disk encryption secures our server certificates, configurations, and other software, so even in the unlikely event that someone was able to get physical access to one of our VPN servers, they would not be able to access its encryption keys.
Keep your connection secure with Proton VPN
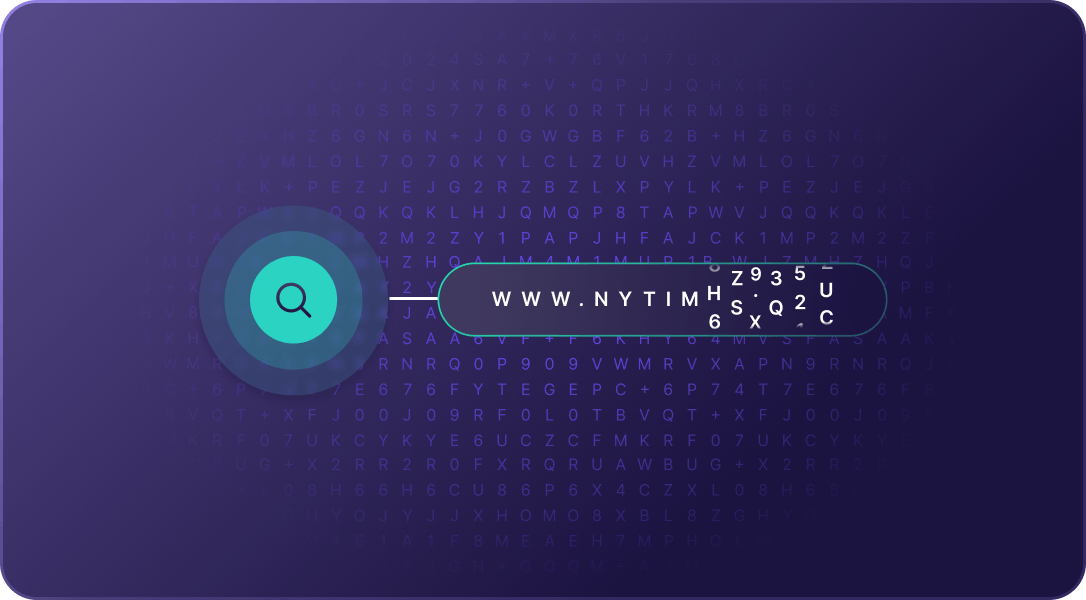
DNS leak protection
Your DNS queries can be analyzed to see what websites you visited. To prevent this, we include your DNS queries in the encrypted VPN tunnel and run our own DNS servers. This ensures your DNS queries are resolved without ever exposing your browsing activity.
Kill switch
Our built-in kill switch feature continuously monitors your connection to our VPN servers and will immediately block all network traffic if you lose your connection to the VPN server. By blocking all traffic, the kill switch feature prevents your true IP address from being revealed.
Tor over VPN
If you have a Plus plan, you can use Proton VPN to access the Tor network. Route all your traffic through the Tor anonymity network and access onion sites with a single click using our Tor-enabled VPN servers.
A secure, trusted VPN
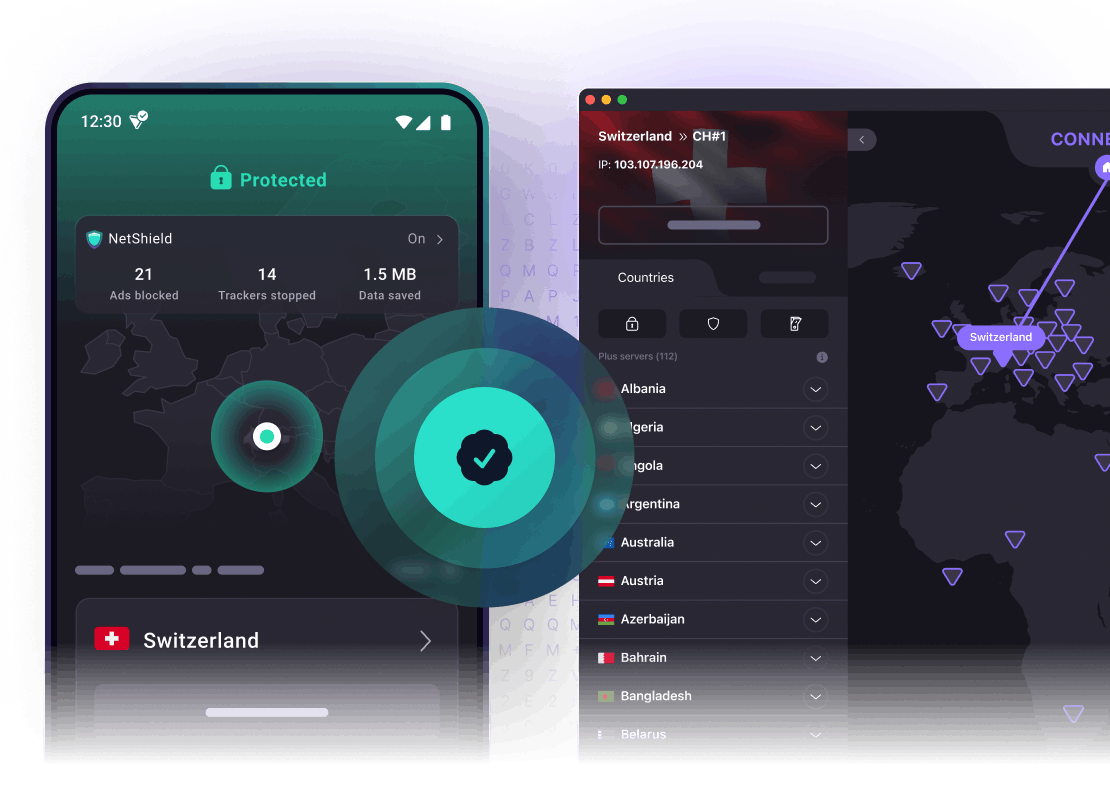
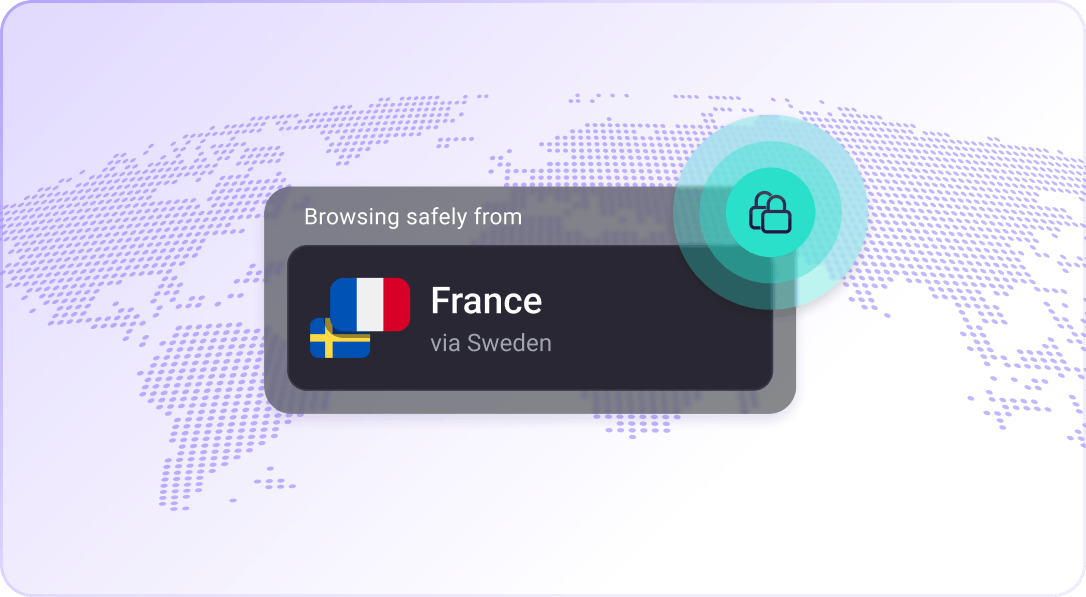
Secure Core VPN
Our Secure Core architecture gives you extra security against advanced attacks by routing your traffic through multiple servers before it leaves our network.
No-logs VPN
We follow a strict no-logs policy (which has been confirmed by independent security experts) to ensure your browsing history stays private and cannot be turned over or shared with anyone.
NetShield Ad-blocker
NetShield uses DNS filtering to find, identify, and block ads, malware, and trackers before your device can load them.
Based in Switzerland
Our headquarters is in Switzerland, where we are protected by some of the world’s strongest privacy laws and remain outside of US and EU surveillance jurisdictions.
Audited by independent experts
We have commissioned professional cybersecurity audits for all our apps and published the full results on our website.
Tor over VPN
Easily access onion sites through Proton VPN. Our VPN servers route your connection through the Tor network with one click.
VPN Accelerator
VPN Accelerator can increase your browsing speed by over 400%. It has the greatest effect on performance when you connect to distant VPN servers.
Easy to use
Use our Quick Connect button to easily connect to the fastest VPN server for your location in a single click.
Secure your internet with Proton VPN
- IPv6 leak protection
- Secure VPN protocols
- Strict no-logs policy
- Advanced encryption
- Block ads, trackers, and malware