Torrenting is an incredibly fast and efficient way to distribute large files over the internet. Although often considered to be synonymous with piracy, there are many legitimate use cases for torrenting. However, before diving into the world of P2P file sharing, you should understand what torrenting is, how it works, and how to protect yourself from some of the risks associated with torrenting.
- What is P2P file sharing?
- What is torrenting?
- How does torrenting work?
- What is torrenting used for?
- Is torrenting illegal?
- What are the risks of torrenting?
- How to protect yourself while torrenting
- How to use torrents
- What to look for in a VPN for torrenting
- Torrenting FAQ
What is P2P file sharing?
P2P, or peer-to-peer, is the term used to describe the locating and sending of files between a network of devices. P2P file sharing uses a decentralized network made up of “peers” that can be used to share information. You can use P2P file sharing to share documents, audio files, video files, or even programs and video games.
Downloading and uploading files via a P2P network uses file sharing protocols such as BitTorrent (rather than using http, as your web browser does) which are particularly useful for downloading large files.
What is torrenting?
Torrenting is a method of downloading files from a P2P network using torrent files or Magnet links. A torrent file acts as an index that tells your computer where files or parts of files are located within the network, and downloads pieces of them from other peers in the network all at once. This can make downloading large files much faster, as you accept parts of a file from multiple sources. Magnet links work in much the same way as torrent files, but without the need to host and download torrent files.
How does torrenting work?
By downloading a file from multiple peers at once, you can achieve much faster download speeds, as you are accepting small pieces of the file you need from multiple sources at once. As you receive those pieces of the file, you are able to simultaneously upload them.
This is how torrenting works:
- You download the torrent file from a website (or click on a Magnet link) which is loaded into your BitTorrent client. The torrent file holds metadata about the files and folders to be distributed, and a list of network locations of trackers for the file you are looking for.
- The BitTorrent client will use the downloaded torrent file to locate parts of the file you are looking for on other computers in the network and begin downloading them.
- All of the computers in the network use some of their available bandwidth to upload part of the file that you are downloading.
Seeders and leechers
When torrenting, you will either be a leecher, or a seeder. You are a leecher when you are downloading files from peers on the network that already have the parts of the file on their device and are allowing people to download from them (you are “leeching” from them). While you are leeching, you are also seeding the parts of the file you have already downloaded — so leechers are usually both seeders and leechers simultaneously.
Once you have downloaded the file, and you begin uploading it for others to use, you will start seeding only (meaning people are now able to “leech” the file from you in its entirety).
The more seeders there are for any particular torrent, the faster the download speed for that torrent will be, as you will be able to accept incoming pieces of your files from more sources.
If there are no seeders for a torrent, it is unlikely that you will be able to download the complete file. You can leave the torrent loaded in your client in the hopes that a seeder becomes available, but unless one comes online, you will not be able to download the entire file.
What is torrenting used for?
Torrenting is often considered to be synonymous with piracy, but there are actually many legitimate and legal reasons to use BitTorrent.
The main reason to use BitTorrent is to download large files, as it is much faster than downloading a hosted file from your web browser. For this reason, BitTorrent is frequently chosen by distributors to allow their users to download freeware, video games, updates, and Linux distros.
Torrenting is also a much cheaper way of distributing large files for free. For example, if you were in a band and wanted to release a free music album to your fans, you would ordinarily be required to host the files yourself — this would require a lot of bandwidth. Instead, by distributing the files via BitTorrent, you would let your fans contribute their bandwidth as they downloaded your files, and save yourself a lot of hosting costs.
Some organizations use torrents internally to transfer large files from server to server. In 2012, Ars Technica reported that Facebook was using BitTorrent for exactly this purpose(new window).
Is torrenting illegal?
As the above examples demonstrate, torrenting itself is not illegal. While it’s true that BitTorrent can be used to illegally download pirated content, this is also true of your web browser. BitTorrent is just another communication protocol, like PPTP (Point-to-Point Tunneling Protocol) or IP (Internet Protocol).
So torrenting is entirely legal, and as long as you are not using it to download copyrighted or other unlawful material, you cannot get in trouble with the authorities for using it.
What are the risks of torrenting?
While torrenting is a great way to download large files quickly and efficiently, it does come with some risks that you should be aware of before you start downloading files, so you can take the appropriate steps to protect yourself.
Your ISP can see your torrenting activity
As is true for much of your online activity (if you’re not using a VPN), your ISP can see when you are sharing or downloading files via a P2P network. Because of the amount of bandwidth required, some ISPs have been known to throttle BitTorrent downloads, leading to reduced download speeds.
Your ISP is also able to record all the data relating to your torrenting activity, which means they are able to hand that information over to the authorities if requested.
Peers on the network can see your IP address
To exchange packets of information with the other peers (seeders and leechers) on the network, your computer needs to share your IP address. This means that the other people you are sharing files with can see your IP address too. Peers on the network can include malicious actors who may attempt to take advantage of you.
Beware of disguised files
Although you should always be careful to make sure you don’t accidentally download dangerous or infected files, it is particularly easy to accidentally download malicious files when you are torrenting. A torrent with a legitimate-seeming filename may actually result in downloading a virus to your computer.
How to protect yourself while torrenting
Just because there are risks, it doesn’t mean that you cannot take steps to ensure you are always safe while torrenting. By following these steps, you can continue to torrent large files quickly and efficiently without risking your privacy or security.
Use a VPN to hide your activity from your ISP
Any time you do not use a VPN, your ISP can see and record data about your online activity, including your torrenting data. This gives your ISP the power to throttle your torrenting bandwidth or to hand over information about your activity to third parties. You can hide your torrenting activity from your ISP by encrypting your traffic with a VPN. As long as you are connected to a VPN server that allows torrenting — such as Proton VPN’s P2P servers — you can continue torrenting without your ISP being able to see or restrict your P2P file sharing traffic.
Use a VPN to hide your IP address from others in the network
Although using a VPN all the time is the best way to protect your privacy, using a VPN when you are torrenting is particularly important to ensure you are hiding your true IP address from other peers in the P2P network. When you connect to a Proton VPN P2P server, your file sharing traffic is routed through the VPN server before reaching the P2P network, keeping your true IP address hidden.
Check the files you download
There are a few actions you can take to avoid downloading a malicious file when torrenting. Many websites where you can download torrents have enabled comments below each torrent. Those comments will usually alert you to any problems with the torrent quality or malicious files included in the torrent. You can also choose a torrent that has a lot of seeders, as the more popular a torrent is, the more likely it is to be safe to download.
Most importantly, when you load a torrent into your BitTorrent client, review all the files included in the torrent before confirming the download to make sure there are not any files that don’t look right. For example, if you are downloading a music file, you should not expect to see any executable files in your torrent (in general, take extra care when downloading executable files, such as .EXE, .APP, .BAT, .SCR). You should also check the size of the files you are downloading — for example, if a torrent reports that a download is 10GB but you are only downloading a single music album, it could be that the torrent includes unnecessary extra files, which could be dangerous.
Using antivirus software will also help to protect your computer from viruses and other malicious files in the event they are accidentally downloaded.
How to use torrents
Download a BitTorrent client
To be able to download torrents, you need a BitTorrent client. A BitTorrent client is a program that enables you to exchange data as a peer in the P2P network. We recommend choosing an open-source BitTorrent client like qBittorrent(new window) and Transmission(new window). The most popular BitTorrent clients are μTorrent(new window) and BitTorrent(new window) (this is a client with the same name as the BitTorrent protocol).
Find a torrent
Now you need to find a torrent you want to download. The website you visit will be different depending on the files you need. For example, if you were looking for Linux ISO torrents, you can find them listed under BitTorrent on the Ubuntu alternative downloads page(new window), or if you wanted to download and watch movies that are in the public domain you could visit the Internet Archive’s collection of feature films(new window).
There are some websites that are specifically designed for hosting torrent files of all types, but many of these are blocked by ISPs to prevent piracy, even though they host a range of completely legal torrents as well. In many cases, using a VPN(new window) will give you access to these websites, and allow you to continue torrenting as normal.
Download the torrent
Once you have found the torrent you would like to download, click the download button. Depending on the website you are using, this may be more difficult than it sounds, as many torrent websites will show a big Download button that takes you to a paid download solution, or through to another website or an ad, while hiding the true Magnet link or torrent file button.
Clicking the (correct) link will download the torrent file that tells your device where to find the parts of the files it needs within the P2P network. Then you can add the torrent file to your torrent client by clicking Add torrent and selecting the torrent file you downloaded.
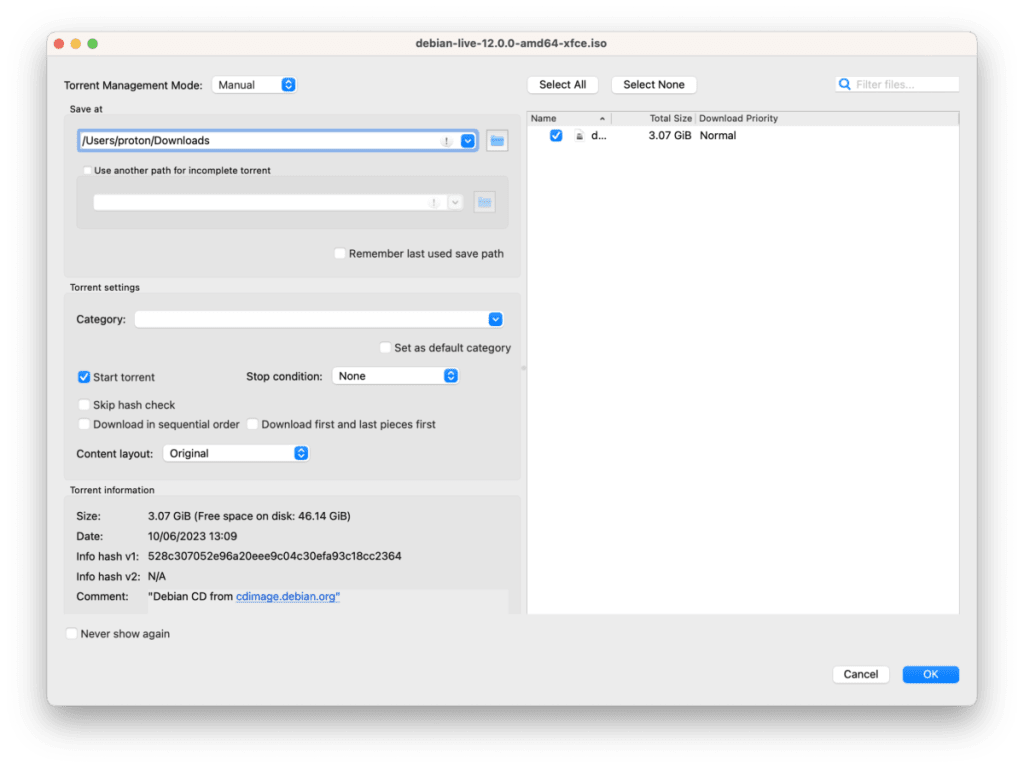
Before confirming the download, make sure that you are downloading the correct files, and that those files are safe, by checking the size, name, and extension of the files you are downloading.
If something doesn’t look right, you can deselect the files you don’t need, or you can abandon the download altogether.
Once you’re happy with the selected files, you can confirm the download. (In the below example, from qBitorrent, you can confirm the download by clicking OK, although the prompt may differ between BitTorrent clients.)
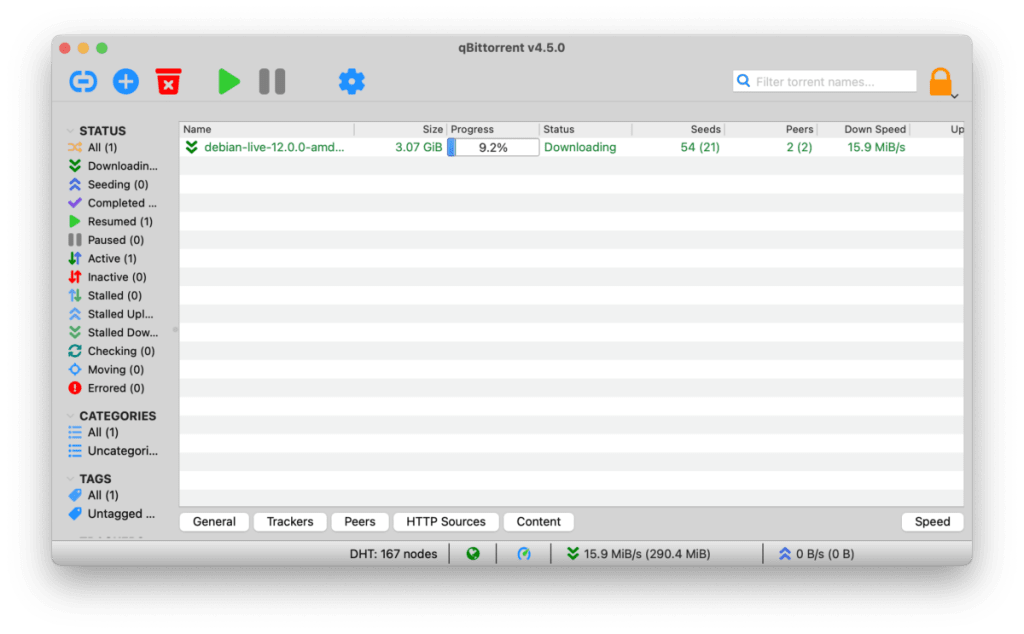
The torrent will then start locating and downloading the files. You will see a progress bar for your torrent as well as various information such as the download and upload speed the torrent is progressing at.
Seed the torrent
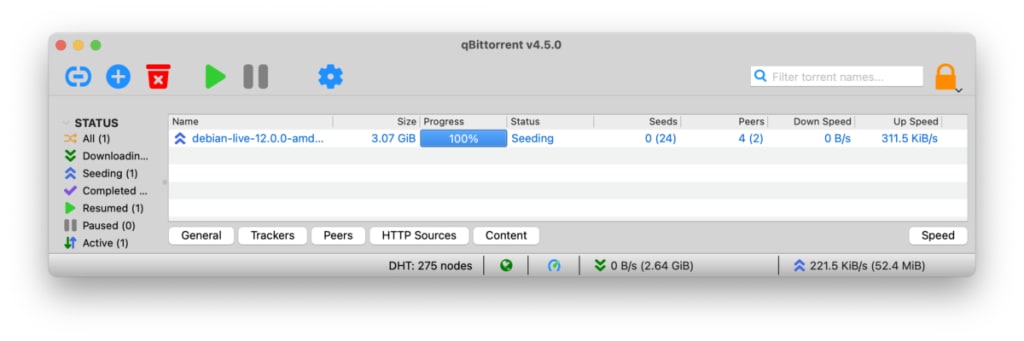
While you are downloading the torrent, your device also becomes a peer in the network. This means torrent files can locate the parts of the file you have downloaded and allow other people to download those same parts of the file from you.
Once you have downloaded the file in its entirety, your torrent client will automatically switch from downloading to seeding. (Although, as stated before, you will usually be uploading parts of a file as you are downloading them simultaneously.) This means that you are now only a seeder in the network and other people can download the file from you in its entirety. Good netiquette demands that people seed the torrents they have downloaded, as without any seeders, P2P file sharing would not be possible.
What to look for in a VPN to use for torrenting
A good VPN will keep your true IP address hidden from others in the network and will prevent your ISP from seeing or throttling your torrenting activity. When looking for the best VPN for torrenting, you should choose one that:
- Does not block P2P traffic
- Does not keep any logs of your activity
- Is not based in a country where logs can be demanded
- Is fast enough to allow for P2P file sharing at a good speed
- Has a kill switch to ensure that your connection is shut off in the event that your VPN disconnects
P2P file sharing with Proton VPN
Proton VPN is a no-logs VPN that protects your privacy. As we are based in Switzerland, we cannot be forced to keep or hand over logs on your VPN activity. (Our latest security audit results confirm our no logs policy.) If you subscribe to a Proton VPN Plus plan, you can take full advantage of our specialized high-speed P2P file sharing servers.
To connect to a server that is optimized for P2P file sharing, look for a server in the Proton VPN app on your device that has the two way arrow icon.

You can then follow the steps above to download large files securely, over our high-speed torrenting VPN servers. For more information about torrenting with Proton VPN, check out our step-by-step support article.
Torrenting FAQ
Yes. You should always hide your IP address while torrenting. Your ISP can see your torrenting activity if you do not use a VPN, and they are also able to hand over this information to third parties. Secondly, when you are connected to a P2P network, everyone else on that network is able to see your IP address. So the best way to stay secure while torrenting is to use a VPN to hide your IP address and online activity.
BitTorrent is a peer-to-peer (P2P) file-sharing protocol that allows your device to communicate and share files with others in the network in a decentralized manner. This means files can be shared without relying on a main server to provide the data.
A torrent is a file that is uploaded and downloaded through a decentralized P2P sharing network via the BitTorrent protocol. Torrenting is the verb for sharing files in this way.
Torrents may work with a free VPN plan, but the best way to ensure you can quickly and safely torrent large files is to sign up for a Proton VPN Plus plan. With a Plus plan you can access our high-speed P2P-optimized servers, ensuring you can torrent quickly and easily without interruptions.
Depending on your provider and the country where you live, you may find that some torrent websites are blocked by your ISP. This is usually to prevent people from downloading pirated content, even though most of these websites also make hundreds of completely legal torrents available. If you use a VPN, you will be able to unblock the torrent sites that are restricted by your ISP.
In torrenting, a “seeder” is the name for a peer on the P2P network who has the completed file for a torrent and is continuing to share that file. A “leecher” is the name of a peer on the network for someone who is torrenting the file from the seeders — they are “leeching” from them. Leechers also seed the parts of the file they have already downloaded as they leech the rest of the parts from others. The more seeders there are for a torrent, the faster you can expect to complete that torrent, as there are more people you can accept pieces of the file from.
P2P stands for Peer-to-Peer. In torrenting, this is the name of the type of technology that allows people to search for and download content in a decentralized way, that is, without relying on a centralized server to provide the files. The unique structure of the network means downloading large files is very efficient.
On a P2P network, the BitTorrent client you are using locates copies of the file that you want to download within that network, and allows your computer to create multiple connections with several sources that have all or part of the requested file.





