“Amazon and third parties (including advertising and tracking services) collect smart speaker interaction data. We find that Amazon processes voice data to infer user interests…

What is a VPN kill switch and when should you use one?
September 15th, 2023 in Privacy deep divesA kill switch is a security feature that protects your privacy. It ensures that you don’t connect to the internet thinking you’re protected by a…

Guest networks – What they are, why you need one, and how to set them up
September 12th, 2023 in Privacy deep divesA guest network is a separate WiFi network within your home or office network designed specifically for your guests or customers to use. Although run…

Can someone see my internet history if we use the same WiFi?
September 1st, 2023 in Privacy deep divesBefore WiFi, you had to connect your internet-capable device to a router via an Ethernet cable. The router then connected to a modem, which connected…

Why use a VPN for business?
August 23rd, 2023 in Privacy deep divesThese days, virtual private networks (VPNs) are most commonly associated with commercial consumer-facing VPN services, such as Proton VPN, that allow individuals to bypass censorship,…

Introducing Proton VPN for Business
August 21st, 2023 in Privacy deep divesToday, we’re happy to announce the official launch of Proton VPN for Business. Since 2016, Proton has been progressively bringing our privacy and security services…

What is Tor Browser?
August 18th, 2023 in Privacy deep divesTor Browser is a privacy-focused browser that lets you navigate the internet without anyone monitoring your activity or identifying you. It relies on the Tor…
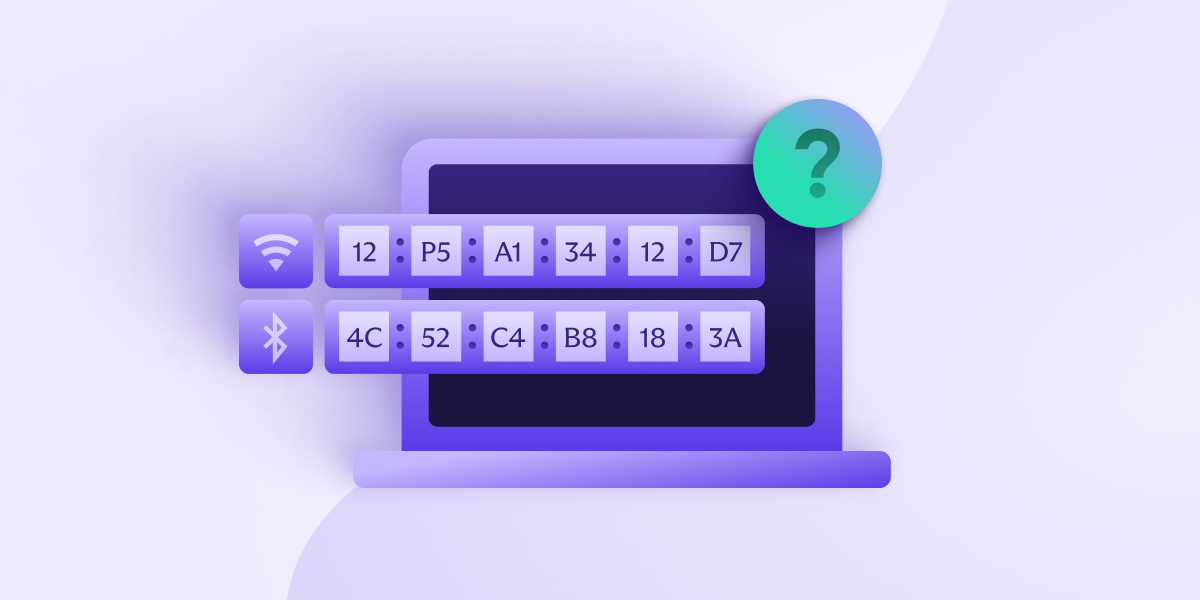
What is a MAC address, and what can it reveal about you?
August 17th, 2023 in Privacy deep divesEvery device that connects to a network does so through a network interface controller (NIC). Devices that can connect to multiple networks will have a…

8 common types of cyberattacks and how to prevent them
July 28th, 2023 in Privacy deep divesHackers are always looking for ways to break through the security systems that defend your devices and data from criminals. From web browsers to operating…
