Update March 2023: While WireGuard continues to officially only support UDP, Proton VPN has now developed an implementation of WireGuard that runs over TCP. In addition to this, our Stealth obfuscation protocol is based on an implementation of WireGuard run over TCP.
OpenVPN and WireGuard® are VPN protocols used to secure the connection between your device and a VPN server.
Learn more about how VPNs work
WireGuard represents cutting-edge VPN technology and is cryptographically secure, highly efficient, and fast.
OpenVPN is beginning to show its age in terms of speed, performance, and efficiency, but remains widely regarded as the most secure and battle-tested VPN protocol available. The ability to run OpenVPN in TCP mode also gives it greater built-in anti-censorship capabilities than WireGuard.
OpenVPN
First released in 2001, OpenVPN is an open-source VPN protocol that uses the OpenSSL library, TLS, plus a variety of other technologies to create a VPN connection that is both secure and stable.
OpenVPN remains the most widely supported protocol by commercial VPN services, although this dominance is beginning to be challenged by WireGuard.
Pros
Secure
Despite being 20 years old, OpenVPN is still widely regarded as the most secure VPN protocol available.
In large part this is due to documents leaked by Edward Snowden in 2013, which showed that the NSA could crack most VPN protocols in use at the time. The documents showed that it could crack OpenVPN, but only(new window) if a pre-shared key was used.
Properly configured OpenVPN with strong encryption settings, certificate-based authentication, and the use of forward secrecy(new window) to ensure each and every VPN session needs to be individually hacked is still considered the gold standard when it comes to VPN security.
Needless to say, Proton VPN uses very strong(new window) OpenVPN settings.
OpenVPN uses two channels to transfer data: the control channel and the data channel.
The control channel
The control channel establishes a TLS connection between the VPN client and the VPN server.
The whole process uses a symmetric key cipher, but the actual key exchange requires an asymmetric encryption system where a public key is used to encrypt the data, which can only be decrypted using a private key.
Proton VPN uses AES-256 for its symmetric cipher, RSA-4096 to ensure a secure key exchange, and HMAC SHA-384 hash authentication to verify the TLS certificates. The encryption suite we use also includes a Diffie-Hellman key exchange (DHE) to provide forward secrecy.
The data channel
Once a TLS connection is established, OpenVPN transfers your actual data over the data channel encrypted with a symmetric cipher (Proton VPN uses AES-256). Proton VPN verifies data transfer during a session using AES-GCM.
Let’s take a closer look at the encryption schemes used by OpenVPN:
AES
AES is a symmetric key encryption cipher, meaning the same key used to encrypt the data is also used to decrypt it. Symmetric ciphers are much faster than asymmetric ciphers, such as RSA, which makes them the preferred choice for encrypting large amounts of data.
Widely regarded as the best symmetric key cipher yet devised, AES is certified by NIST(new window) and is used by the United States government to secure its data. AES has a maximum key size of 256-bits (AES-256), with the US government deeming AES-192 and higher sufficient to secure “top secret” information.
AES-GCM
AES in OpenVPN can now be used in AES-CBC (Cipher Block Chaining) or AES-GCM (Galois/Counter Mode) modes. Like the ChaCha20-Poly1305 cipher used by WireGuard (see below), AES-GCM is an authenticated encryption with associated data(new window) (AEAD) cipher.
This allows it to both secure data and authenticate it, removing the need for authentication using HMAC SHA. AEAD ciphers are also more efficient (and therefore faster) than SHA and have less of an overhead.
Proton VPN uses HMAC SHA to authenticate a connection, but uses AES-GCM to authenticate data for the rest of the session.
Diffie-Hellman Exchange
AES provides highly robust encryption, but if you want to send the data somewhere, you need a secure way to agree on a key.
Asymmetric encryption achieves this using public-key cryptography — the data is encrypted using a public key, which is openly published, but which can only be decrypted by the intended recipient using the correct (secret) private key.
Asymmetric encryption is very slow compared to symmetric encryption systems, such as AES, so it is primarily used simply to authenticate the connection between the VPN client and server.
A Diffie–Hellman key exchange (DHE) is a way to secure the TLS key exchange across an insecure channel (such as the internet). Indeed, OpenVPN can use DHE in this way.
However, DHE at lower key sizes is vulnerable to logjam attacks(new window) thanks to its reuse of a limited set of prime numbers, making its use to secure TLS key exchanges somewhat controversial (even where larger “safe” key sizes are used).
The big advantage of using a Diffie-Hellman exchange over RSA (see below) is that it provides forward secrecy, generating new encryption keys for each VPN session. Without forward secrecy, an adversary who obtains a VPN session’s encryption key will be able to decrypt all historic sessions secured using that key.
Fortunately, OpenVPN’s encryption suite makes it possible to secure the key exchange with RSA, while using DHE just to provide forward secrecy.
RSA
RSA is an asymmetric cryptosystem commonly used to secure TLS key exchanges. In OpenVPN, a DHE key exchange is then performed to agree on a (symmetric) key that secures the data.
There is no theoretical limit to key size length for RSA, but overlong key lengths result in a high computational overhead, and are thus slow and wasteful. Proton VPN implements RSA with a 4096-bit key size, which is sufficiently secure (by a fair margin) while also practical.
HMAC SHA
SHA is a cryptographic hash function used to authenticate data. When performed on any dataset it creates a unique fingerprint. If even one tiny bit of that data changes, the SHA fingerprint also changes, making it very useful for ensuring that data has not been tampered with.
Among its many uses, SHA prevents man-in-the-middle attacks during a TLS key exchange by validating the TLS certificates used during the exchange.
SHA-1 (a 160-bit hash function) is no longer considered secure, but SHA-2 is. OpenVPN only uses SHA to calculate hash message authentication code(new window) (HMAC) values anyway. These are much harder to attack than the SHA algorithm on its own, to the point where even SHA-1 is still considered secure enough for HMAC.
Audited
OpenVPN was independently audited(new window) by OSTIF and QuarksLab in 2016 following a successful crowdfunding campaign. One critical/high vulnerability was discovered, but this concerned susceptibility to a denial of service, and did not impact the security of users. It was also patched before the report was made public.
Anti-censorship capabilities
OpenVPN can be run over either UDP or TCP. UDP is faster, while TCP is more reliable, but the main advantage is that TCP is useful for defeating censorship by governments and other organizations.
By default, we route OpenVPN TCP connections over port 443. This is the port used by the HTTPS protocol that secures all sensitive communications on the internet, including online banking logins and shopping. It is therefore very difficult to block this port without “breaking” the internet.
It should be noted, though, that advanced deep packet inspection techniques can detect OpenVPN, no matter which protocol or port number is used.
Cons
When compared to the lightweight elegance of WireGuard, OpenVPN is relatively inefficient. It uses much more processing power than WireGuard, which makes it slower, especially on lower-powered devices.
The extra processing power required also means that OpenVPN drains batteries faster than WireGuard.
WireGuard
Work on WireGuard began in 2016, quickly catching the interest of the VPN community (Proton VPN has supported the project since 2018). In March 2020, WireGuard 1.0.0 stable was announced, together with news(new window) that it would be merged into the 5.6 Linux kernel.
It is now also a stable release on all major platforms, including Windows, macOS, BSD, iOS, and Android. Public reception has been very positive, with support for WireGuard being one of our most requested features.
Pros
Fast
The Advanced Encryption Standard instruction set(new window) (AES-NI) is built-in to many modern processors, greatly improving the speed at which AES instructions can be processed. Since OpenVPN most often uses AES as its symmetric key encryption cipher, it benefits from this cryptographic hardware acceleration(new window).
WireGuard enjoys no such dedicated hardware support (at least for now), but despite this, offers speeds comparable to hardware accelerated AES. This is partly due to the fact that it can leverage generalized hardware support for vectorized operations (for example using the SSE and AVX(new window) processor extensions).
Going forward, it is expected that the gap between ChaCha20-Poly1305 and AES with AES-NI will become smaller (or even that ChaCha20-Poly1305 may even become faster).
WireGuard also connects much faster than OpenVPN, typically taking less than one second to establish a connection to a VPN server.
Efficient
The core WireGuard protocol consists of just a few thousand lines of code, making it extremely lightweight. In addition to improved performance on low-end hardware, this translates to better battery life when running on devices, such as mobile phones and laptops.
Secure
WireGuard uses an amalgam of state-of-the-art cryptographic primitives to secure the VPN connection.
- ChaCha20(new window) — A symmetric key cipher. Much like AES on OpenVPN, ChaCha20 secures your actual data.
- Poly1305(new window) — A message authentication code(new window) (MAC) used to authenticate WireGuard connections.
- Curve25519(new window) — An elliptic curve(new window) used by the Elliptic-curve Diffie–Hellman(new window) (ECDH) protocol to secure the TLS key exchange. This ensures your connection to our VPN servers is secure.
- SipHash(new window) — An XOR(new window)-based pseudorandom hash function used to securely map hash table(new window) keys.
- BLAKE2(new window) – A cryptographic hashing function used to verify data.
These are all regarded as proven cryptographic standards, and WireGuard is widely regarded as a highly secure VPN protocol by cryptographic experts.
Audited
WireGuard’s lightweight nature (just a few thousand lines of code) is a serious boon when it comes to auditing the protocol.
WireGuard has undergone(new window) a series of formal verifications(new window) and computational proofs covering aspects of its cryptography, protocol, and implementation.
The protocol itself has been verified using the open-source Tamarin Prover(new window) security protocol verification tool, which anyone can re-run for independent verification.
In addition to all this, to be incorporated in the Linux kernel, the WireGuard Linux codebase was independently audited(new window) by a third party. No vulnerabilities were found, although “a good defense-in-depth suggestion” was made by the auditing team.
Cons
Security is theoretical
The math says WireGuard is a very secure VPN protocol, but it is still new, and has not proven itself in the field in the way OpenVPN has.
No built-in anti-censorship capabilities
WireGuard uses the User Datagram Protocol (UDP) and does not support use over the Transmission Control Protocol (TCP), which makes it trivial to detect and block.
The good news is that it is possible (in theory at the present time) to add obfuscation techniques on top of WireGuard to improve its resistance to censorship.
Privacy requires additional work from VPN providers
Out of the box, WireGuard offers security, but not necessarily privacy. This is because WireGuard was designed to create one-to-one static VPN connections between the client (VPN app) and the VPN server.
Proton VPN addresses this issue by hardcoding our apps to begin every WireGuard VPN connection with the same internal IP address (10.2.0.2).
WireGuard’s design also means that, out of the box, it is not suitable for commercial VPN deployment where multiple users connect to the same VPN server at once.
Proton VPN solves this issue and strengthens our privacy protections by using double network address translation (double-NAT) to dynamically provision sessions.
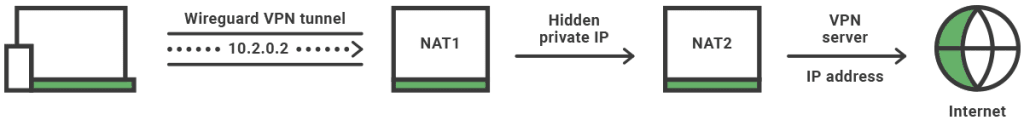
This means that when your Proton VPN app connects to one of our VPN servers via WireGuard, the first NAT will rewrite the 10.2.0.2 IP address to a random but unique internal IP address that is assigned to your session.
From this point on, WireGuard works like any other VPN: The second NAT rewrites your session IP address again to the VPN server’s public IP address before it connects to your desired website.
When you connect to a Proton VPN server via WireGuard, your device and our VPN server can only see the IP address 10.2.0.2, and any website you visit can only see the public IP address of our VPN server.
With these innovations in place, your true IP address remains just as secure and private as it does when using OpenVPN.
Supported on fewer devices
WireGuard is now officially supported on all major computer operating systems (Linux, Windows, macOS, BSD, iOS, and Android), but it is not well supported on other devices.
Many routers include an OpenVPN client, for example, but although available as an experimental package(new window) for pfSense, support for the new protocol on router firmware is basically non-existent (for now, anyway).
So… which is better, OpenVPN or WireGuard?
Proton VPN now uses WireGuard by default because it is secure while also being faster and more efficient than OpenVPN. Under our implementation, it is also just as private as OpenVPN. We therefore believe it is the best VPN protocol for most of our users most of the time.
However, there are situations where OpenVPN may be the preferred option:
- Where security is a very high priority — OpenVPN’s battle-proven nature gives it the edge over WireGuard’s more theoretical security credentials.
- To defeat censorship — the ability to run in TCP mode gives OpenVPN greater resilience to censorship.
- When using devices that don’t support WireGuard — this applies particularly to running a VPN on routers.
Frequently asked questions
IKEv2 remains a good, fast, and secure VPN protocol, and Proton VPN continues to support it for these reasons. However, it has to be said that there is little reason to choose IKEv2 over WireGuard.
PPTP is an obsolete VPN protocol whose security weaknesses make it unfit for purpose. We do not think any responsible modern VPN service should offer PPTP as an option to its users.
Learn more about PPTP
L2TP/IPsec remains widely used and is still broadly considered secure, despite evidence that it has been cracked by the NSA and that it was deliberately weakened(new window) during its design phase. The common practice among some commercial VPN services of using pre-shared keys(new window) is also a concern.
The bottom line, however, is that L2TP/IPsec offers no advantage over more modern VPN protocols, such as IKEv2 and WireGuard, while also not offering the tried and tested security and anti-censorship capabilities of OpenVPN.
SSTP uses SSL 3.0 to secure VPN connections. It offers many of the advantages of OpenVPN, and as a Microsoft-developed standard, benefits from tight integration with Windows.
However, it is a proprietary standard, and concerns over SSL 3.0’s vulnerability to POODLE attacks(new window) (which may or may not affect SSTP) have done nothing to inspire confidence in the standard.





