What is Secure Core?
Proton VPN has a Secure Core feature that improves user privacy and data security by mitigating some of the risks from a compromised VPN server.
A common method to expose VPN traffic is to compromise the server that handles your traffic. This risk is particularly acute for servers located in high-risk jurisdictions.
To mitigate this risk, Proton VPN has Secure Core servers. This article provides an overview of the attacks and threats that Secure Core mitigates, how it achieves higher VPN privacy, as well as instructions on how to activate Secure Core on:
What does Secure Core protect against?
Proton VPN’s unique Secure Core architecture allows us to protect our users from network attacks that other VPNs cannot defend against. A classic VPN setup involves a client passing traffic through a VPN server en-route to the final destination. If an attacker can get control of the VPN server, or monitor the network of the server, they will be able to match VPN clients with their traffic, nullifying the privacy benefits of the VPN.
Such timing/correlation attacks are not difficult to accomplish. In countries with restrictive Internet regulations (China, Russia, Iran, Turkey, etc.), or countries with broad surveillance powers (USA, UK, etc.), state surveillance agencies typically have the legal ability to coerce either the VPN provider, or the network/server provider of the VPN provider, to assist with such network monitoring. Therefore, even though Proton VPN is based in Switzerland, we cannot be certain that authorities are not monitoring our VPN servers located in those high-risk countries.
How does Secure Core increase VPN privacy?
Secure Core allows us to defend against this threat to VPN privacy by passing user traffic through multiple servers. When you connect to a server in a high-risk jurisdiction like the US, your traffic will first go through our Secure Core servers. Therefore, even if an attacker monitors our servers in the US, they would only be able to follow the traffic back to the edge of our Secure Core network, thus making it far more difficult to discover the true IP address and location of Proton VPN users.
We have also gone to extraordinary lengths to defend our Secure Core servers. First, servers are located in countries selected specifically for their strong privacy laws (Iceland, Switzerland, and Sweden). We also placed our Secure Core servers in high-security data centers to ensure strong physical security. Proton VPN infrastructure in Sweden is housed in an underground data center, while our Iceland servers are on a former military base. Furthermore, Secure Core servers are wholly owned and provisioned by us (shipped on-site directly from our offices). Finally, Secure Core servers are connected to the Internet using our own dedicated network with IP addresses that are owned and operated by our own Local Internet Registry (LIR).
These measures provide us with a much higher level of certainty that no one has tampered with our Secure Core servers. While there is no such thing as 100% security, Secure Core is just one of the many ways Proton VPN delivers better security and privacy by protecting against complex attacks other VPNs cannot defend against.
How do I use Secure Core?
Secure Core is a feature available on all paid Proton VPN plans and can be activated as follows:
Windows
1. Open the Proton VPN app onto the Home screen. Select the Countries → Secure Core filter tab to see the list of countries that support Secure Core.
2. Select a Secure Country. This is the location you will appear to access the internet from. If you simply select a Secure Core country, your connection will be automatically routed via the best Secure Core server location (Iceland, Sweden, or Switzerland) for your chosen country.
If you prefer, click ⏷ next to the country to select a Secure Core server location from the dropdown list. (Note that not all Secure Core countries support all Secure Core server locations.)
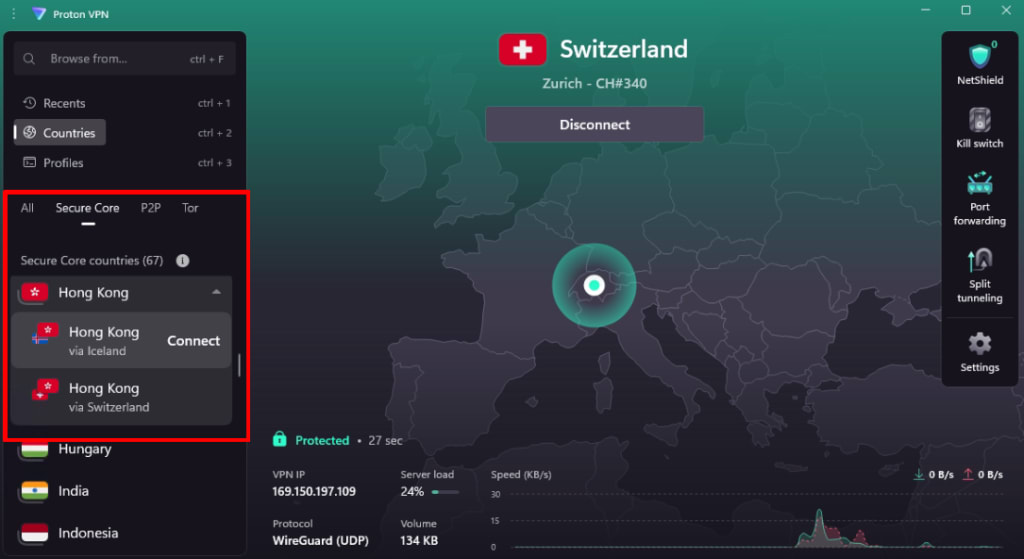
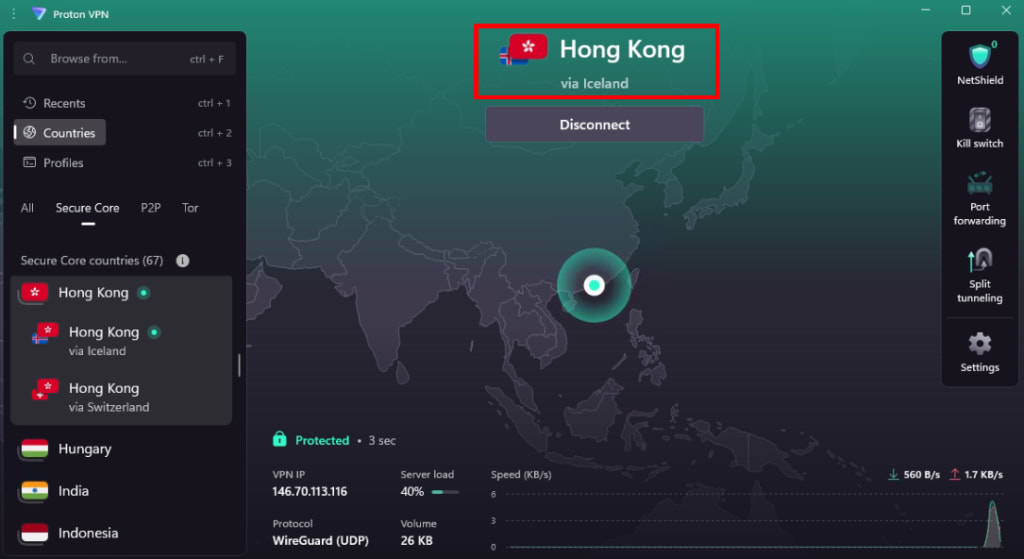
Once the connection is established, the Secure Core routing details will be clearly displayed on the Home screen.
macOS
1. Open the Proton VPN app, click on the Secure Core button, and select Secure Core On.

2. Select a country and click Connect to connect to it via one of our Secure Core servers. Alternatively, you can click the ∨ dropdown button next to a country and choose a Secure Core server to route your connection through.

Please note that not all countries can be connected to from all of our Secure Core locations.
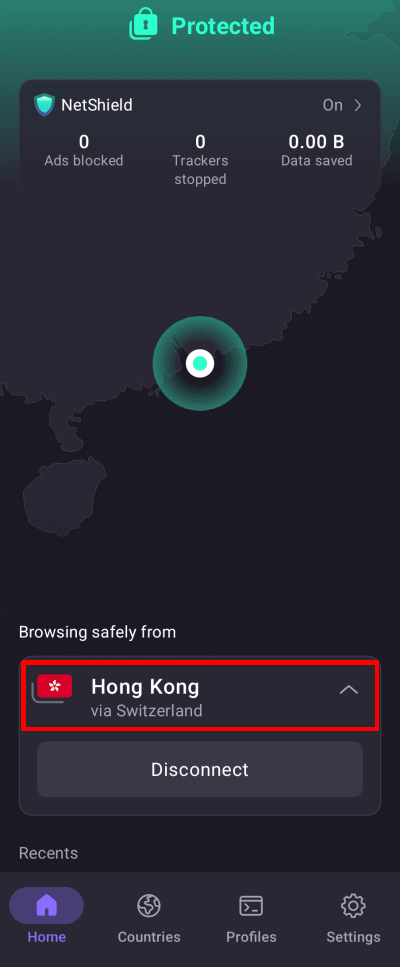
Android
1. Open the Proton VPN app and go to Countries tab →Secure Core filter tab to see the list of countries that support Secure Core.
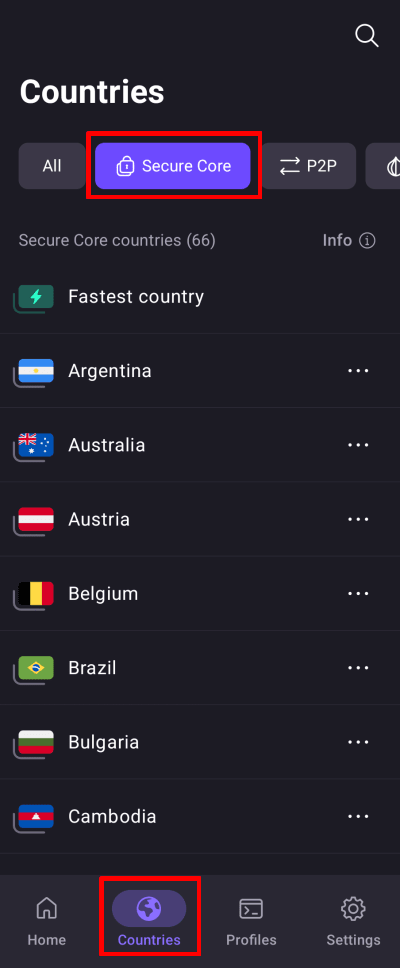
2. Select a Secure Country. This is the location you will appear to access the internet from. If you simply select a Secure Core country, your connection will be automatically routed via the best Secure Core server location (Iceland, Sweden, or Switzerland) for your chosen country.
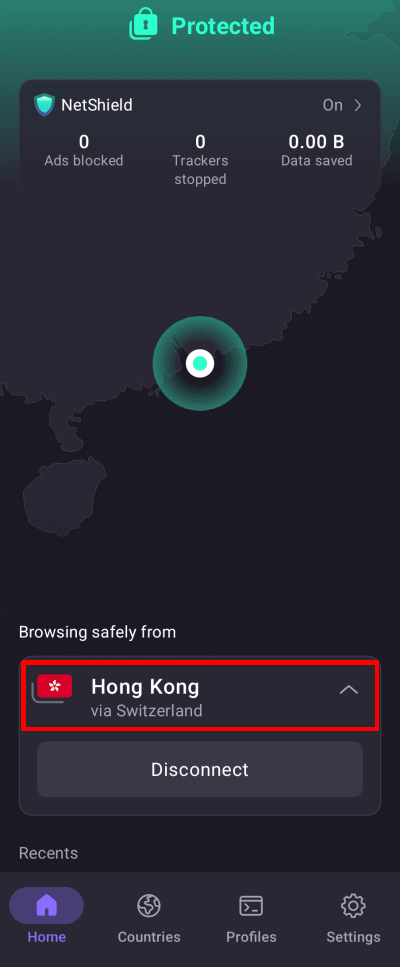
Once the connection is established, the Secure Core routing details will be clearly displayed on the Home screen.
If you prefer, tap ⋯ next to the country to select a Secure Core server location from the list. (Note that not all Secure Core countries support all Secure Core server locations.)
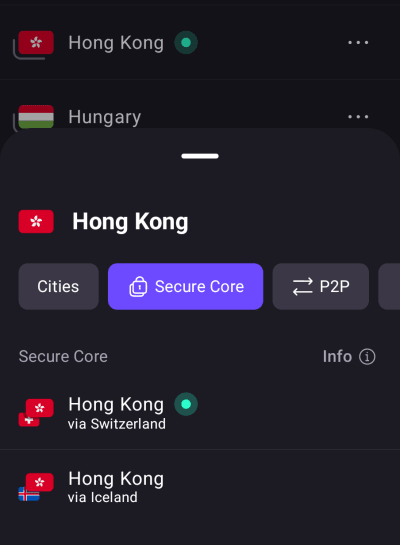
iOS and iPadOS
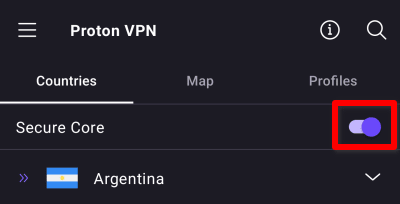
1. Open the Proton VPN app and toggle the Secure Core switch on.
2. Tap on a country you wish the VPN to exit from, and then tap the on button next to the Secure Core country you want the connection to be routed through.
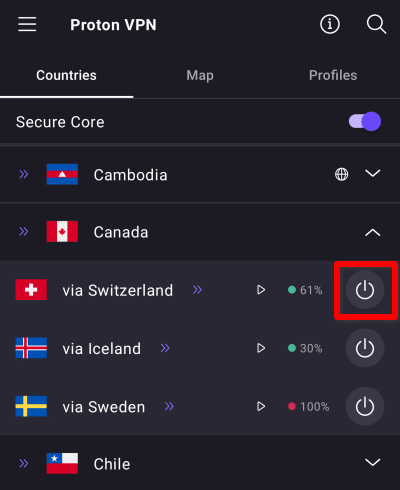
Please note that not all countries can be connected to from all of our Secure Core locations.
Linux
On our Linux app, Secure Core servers are currently shown in the server list for each supported exit country. Secure Core servers have two Alpha -2 ISO country codes(new window), signifying entry location-exit server.
For example, CH-LU#1 indicates a Secure Core server, where the entry sever is located in Switzerland and the exit server is LU#1 (located in Luxembourg).

To see the full list of Secure Servers, enter – into the search bar.
