Bloatware is unwanted software pre-installed on new PCs, laptops, and mobile devices by the device manufacturer, OS developer, or network carrier. It is not usually malicious, but it uses up system resources and can therefore slow down your device.
Most software people think of as bloatware is third-party trial software that is either time-limited or has other restrictions that can only be removed by purchasing the full product or subscription.
It is typically loaded onto devices by OEM manufacturers as part of a business deal with the software’s developers, who hope that once the new owners have tried using their software, they will pay to continue using it.
In some cases, this business model is fairly harmless, but in others, most notably the practice of bundling expensive and unnecessary antivirus software on new PCs, it can be viewed as highly exploitative, preying on the ignorance of less tech-savvy users who may feel obliged to upgrade for fear that “bad things” might happen if they don’t.
Is bloatware a security risk?
Bloatware can be annoying, as the unnecessary apps use up memory and processing power, and can thus slow your device down. Most of it isn’t actually harmful, although there are some exceptions.
Adware
Some bloatware is little more than malware that sends a lot of information back to its developers, which is then used to target you with personalized ads. Some more aggressive adware apps may even show pop-up ads on your device’s screen.
The most notorious example(new window) of this was laptop manufacturer Lenovo pre-installing Superfish(new window) spyware on its machines. Since 2014 concerns had been raised about the way in which Superfish Visual Search software scanned SSL-encrypted traffic on machines sold by Lenovo.
This already bad situation escalated dramatically in February 2015 when Superfish software installed a self-signed certificate authority(new window), which allowed a man-in-the-middle attack(new window) to show Lenovo users ads even on SSL-encrypted pages.
The certificate authority used the same private key(new window) across laptops, which allowed Superfish to intercept users’ HTTPS(new window) secure communications without triggering any browser warnings.
It also opened up the possibility of criminal hackers extracting the private key(new window) used by Superfish and using it to sign their own certificates, which they could then use to spy on Lenovo users if they were on the same network (such as the public WiFi at a coffee shop).
Microsoft quickly responded by releasing an update for Windows Defender(new window), which removed Superfish. A class action lawsuit was filed against Lenovo over the incident, resulting in the company paying $7.3 million in damages to customers who had been affected. In 2017, it was forced to make another settlement with the FTC(new window), in which it also agreed to be monitored by the FTC for 20 years.
Apps with vulnerabilities
All software can potentially contain accidental vulnerabilities that can be exploited by malicious actors, but software of dubious provenance, such as bloatware, is likely more susceptible to this than most.
Are OS apps bloatware?
Most commercial operating systems come bundled with a suite of apps developed by the OS developer (Apple, Microsoft, or Google). These are generally well-made, pose no security risk, and integrate well with other bundled apps and the operating system itself.
But they are still apps you may not want or ever use. Arguably the litmus test of whether these default apps can be considered “bloatware” is whether the OS developer allows you to uninstall them without jumping through arcane hoops.
On Android, Google includes a number of stock apps as part of the OS, such as the Chrome browser, which can be disabled but not fully deleted.
The situation is further complicated by Android being an open-source operating system.
This allows device manufacturers to modify the base OS, replacing Google’s apps with their own (usually inferior) versions, which you also can’t uninstall. Samsung is particularly notorious for this practice.
Android manufacturers also tend to bake third-party apps, such as Facebook Messenger, into the modified OS as part of licensing deals. And unlike on Windows, these cannot be completely uninstalled.
Platforms with no bloatware
Linux
Many Linux distributions bundle apps that the distro developers think might be useful to users. However:
- These apps are almost invariably non-commercial open-source (FOSS) software
- They can be easily uninstalled
- There are plenty of bare-bones distros that include few or no pre-installed apps (on Arch Linux, for example, you effectively build your open OS, selecting every package you wish to install).
ChromeOS
Although built on Gentoo Linux, ChromeOS is basically the Chrome browser as an operating system. Everything happens inside the browser, and there are no “ChromeOS apps” that could constitute bloatware.
Most modern Chromebooks can now also run Android apps, and new machines come with some Google Android apps pre-installed. It should be noted that, as per regular Android, some of these cannot be uninstalled.
How to uninstall bloatware from Windows 10 and Windows 11
Third-party software
Bloatware is most strongly associated with third-party software and custom utilities pre-installed on Windows machines by PC and laptop manufacturers. The good news is that removing this unwanted software is easy (see below).
Microsoft software
Microsoft has made it easier to remove some of its software from Windows, but software it considers “core” to the Windows experience must be removed using PowerShell (we don’t recommend using third-party “cleaner” tools, as these are typically crapware that cause more problems than they solve).
Cortana can be disabled(new window) and hidden(new window), but cannot be removed.
Many Microsoft apps are easy to remove from Windows. These include:
- 3D Viewer (previously called Mixed Reality Viewer)
- Candy Crush
- Cooking Fever
- Disney Magic Kingdoms
- Groove Music
- Movies & TV
- Mixed Reality Portal
- Office
- OneNote
- Paint 3D
- Skype
- Snip & Sketch
- Sticky Notes
- Tips
- Voice Recorder
- Weather
- Bbox
- Xbox Live
To remove third-party or uninstallable Microsoft apps from Windows 10 or 11:
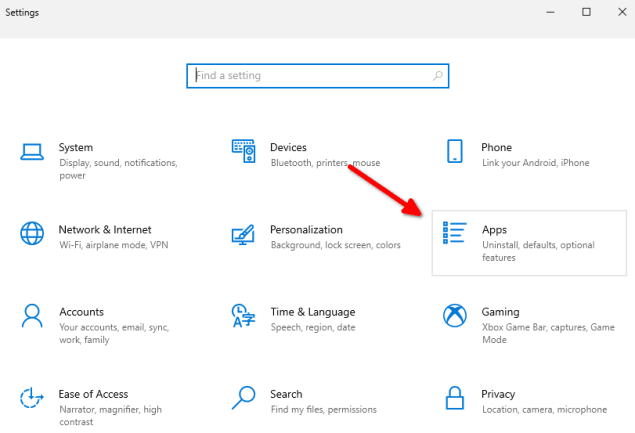
1. Press Win + I to open Settings → Apps (in Windows 11 this can be found in the left pane).
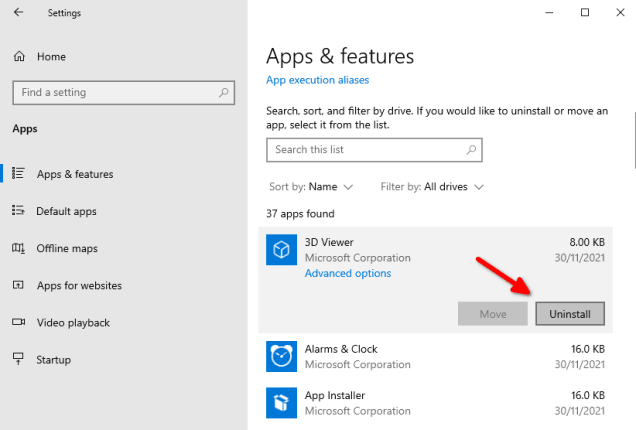
2. Scroll down the list to find an app you wish to uninstall, click on it → Uninstall (or right click → Uninstall in Windows 11).
You can remove most other default apps (except Cortana) using PowerShell.
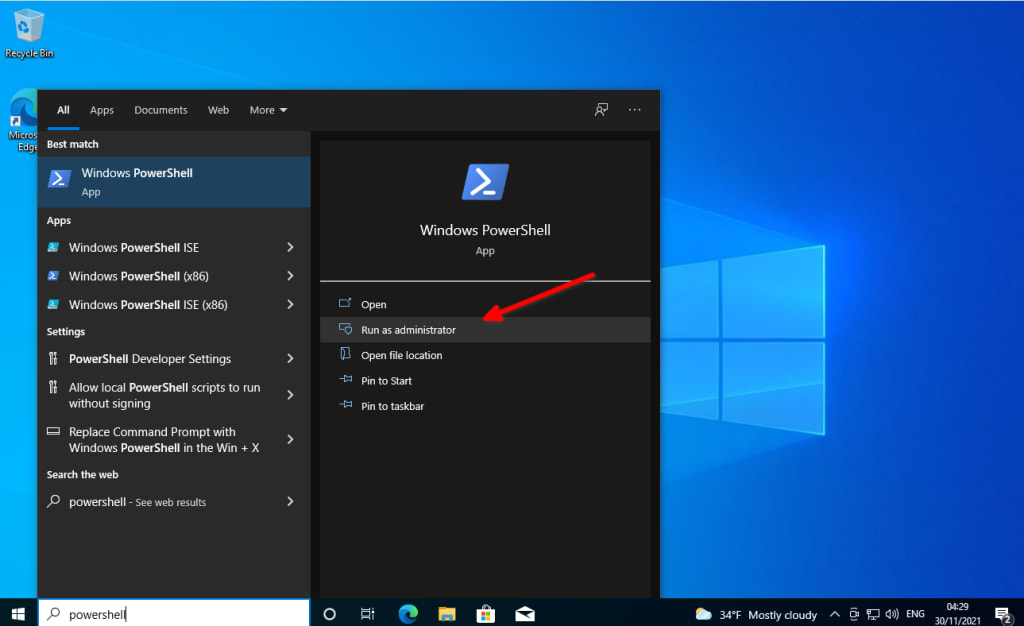
1. Click Start and type powershell into the search box. When the app appears in the search results, Run as administrator.
2. Paste in the following command and hit enter. This lists all non-essential Windows packages (bloatware) installed on your system.
DISM /Online /Get-ProvisionedAppxPackages | select-string Packagename
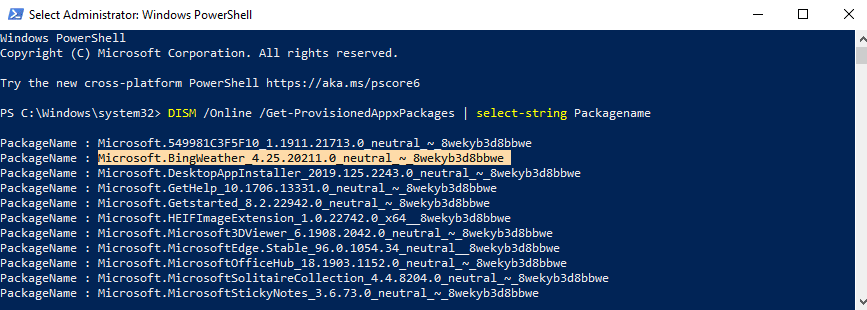
Scroll through the list to find the name of the app you wish to remove, or right-click on the PowerShell title bar → Edit → Find and enter the name of the app you want to uninstall. For example, Microsoft.BingWeather_4.25.20211.0_neutral_~_8wekyb3d8bbwe.
Then enter:
DISM /Online /Remove-ProvisionedAppxPackage /PackageName:[packagename]
For example:
DISM /Online /Remove-ProvisionedAppxPackage /PackageName:Microsoft.BingWeather_4.7.20002.0_neutral_~_8wekyb3d8bbwe
How to remove bloatware from macOS
Apple never bundles third-party software with new Macs, and the suite of default apps it does include with macOS are of very good quality. However, many people have no use for apps, such as Stocks, Podcasts, or iMovie, or may prefer third-party alternatives to Pages, Music, and Maps.
Unfortunately, there is no easy way to uninstall these default apps on macOS. Technically, it is possible to remove macOS’s System Integrity Protection(new window) (SIP) and then remove default apps using Terminal commands, but we strongly recommend against doing this.
Removing SIP leaves your Mac open to malicious code being executed, and removing default apps can have unforeseen consequences for the stability of your system.
iOS
Conversely, since iOS/iPasOS 14, Apple has made it easy to remove many of its default apps from iOS and iPadOS (and, of course, it never bundles third-party apps with new iPhones and iPads).
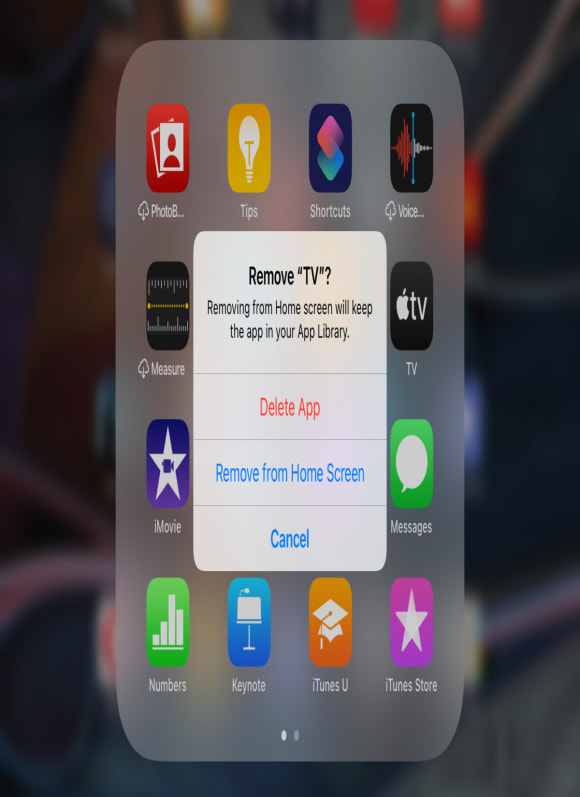
Apple has published an official list of apps that you can remove from iOS and iPadOS(new window). To uninstall an app:
1. Touch and hold the app
2. Tap Remove App
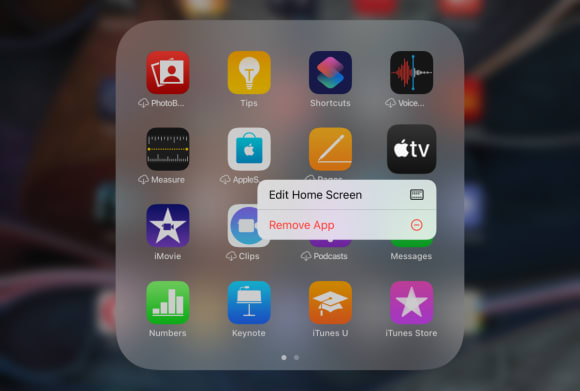
3. Tap Delete App
How to remove bloatware from Android
You cannot easily completely remove Google’s apps from Android devices, but you can disable many of them. This, at least, ensures they use minimal system resources.
Depending on your device’s manufacturer, it might be possible to remove pre-installed apps in the regular way, but it is common practice for manufacturers to lock many of these down so that, like Google’s apps, you can disable, but not entirely remove them.
How to remove or disable system apps on Android
Details on how to disable system apps can vary by device manufacturer. See below for additional information on Samsung devices.
1. Go to Settings → Apps and tap on the app you wish to uninstall.
2. At the bottom of the screen, tap Force Stop. If the app is running,you need to stop it before you can uninstall or disable it.

3.Tap Uninstall (if available) or Disable.

How to remove bloatware from Samsung Galaxy devices
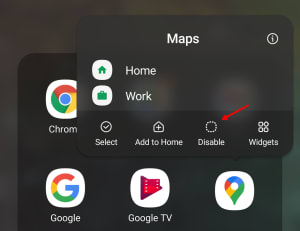
You cannot uninstall Samsung apps via the Android Settings app drawer, but you can uninstall many of them via the app drawer. You can also disable many Google apps using this method.
1. Swipe up from the Home screen to open the app drawer.
2. Select the app you would like to uninstall or disable, long-press on it → Uninstall or Disable.
Other options
If it is not possible to uninstall or disable a system app using the Android user interface, you can remove most apps from your device using Android Debug Bridge(new window) (ADB). This is a powerful command-line tool used by developers to debug their Android apps.
Most apps can be uninstalled in this way, although they will only be removed for the current user. This means the app still resides on your device, and will be available to other users (such as a guest user) when they log in to your device.
The only way to 100% eradicate system apps is to root(new window) your device. We do not recommend doing this for various reasons, and therefore do not provide instructions in this guide. If you wish to take this route, please be aware that it is very easy to do irreparable damage to your device in this way.
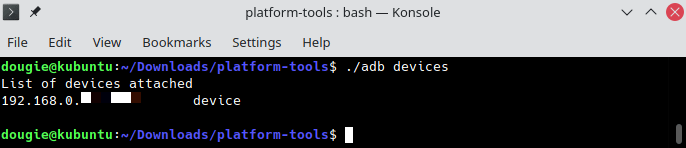
How to remove Android apps using ADB (no root)
Note: On macOS, or if you have fully installed ADB on your desktop system (rather than simply unzipped the Android SDK Platform Tools into a folder, as described in these instructions), you do not need to prefix adb commands with ./ .
1. Enable USB debugging (new window)on your Android device.
2. Download the Android SDK Platform Tools ZIP file for Windows(new window), macOS(new window), or Linux(new window).
3. Unzip the file to a location of your choice. This can be anywhere, but we’ll assume the folder containing the Android SDK Platform Tools is called platform-tools.
4. Open a command-line at the folder you have just created:
- Windows — open the platform-tools folder in Explorer, Shift + right-click → Open Powershell window here or Open command window here
- macOS — open the Terminal app and type cd. Drag the platform-tools folder from Finder to the Terminal window to complete the path to the tools and click enter.
- Linux — navigate to the platform-tools folder in your preferred file manager and open a terminal window here (details vary by file manager – in Nautilus right-click → Open in Terminal, in Dolphin right click → Open Terminal here, etc.).
5. Attach your Android device to your desktop system using a USB cable (in MTP mode(new window), although this doesn’t matter for all devices). It is also possible to connect wirelessly(new window).
6. Type:
adb devices <enter>
This will start the ADB service and ensure your device is connected correctly. If this is the first time using ADB with your device, you will be asked to authenticate the connection on your device. You should see the IP of your device in the List of devices attached output.
7. Find the package names of apps installed on your device using the following commands:
To list all apps:
./adb shell pm list packages
To list only system apps:
./adb shell pm list packages -s
To list only apps from the OEM manufacturer, network carrier, or by app name.
pm list packages | grep ‘<OEM/Carrier/App Name>’
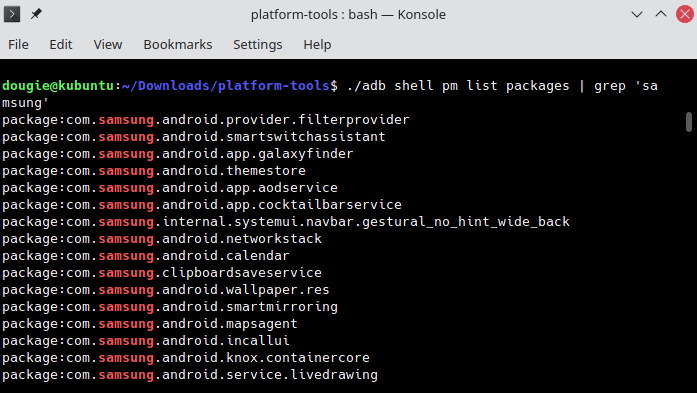
For example, to list all Samsung apps on a Samsung phone, enter:
./adb shell pm list packages | grep 'samsung'
Alternatively, the App Inspector(new window) app can be used to obtain app package names.
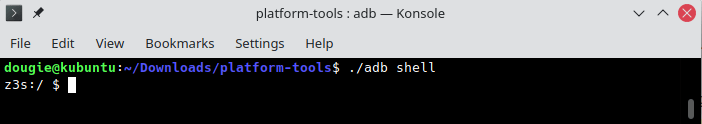
8. To run commands on your device, enter:
./adb shell
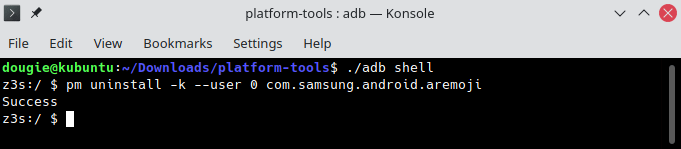
9. To uninstall the app but keep app data and its cache, run:
pm uninstall -k --user 0 <packagename>
To uninstall the app and all app data, run:
pm uninstall --user 0 <packagename>
For example, to remove Samsung’s gimmicky AR Emoji stickers app (but keep the app data), run:
pm uninstall -k --user 0 com.samsung.android.aremoji
A full list of bloatware packages (sourced from the Samsung community forum(new window)) that it is safe to uninstall from Samsung Galaxy phones can be found here(new window).
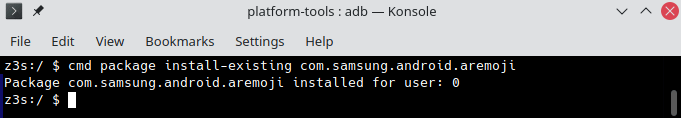
We mentioned earlier that, even using the ADB method, apps are only removed for the current user (–user 0). If you wish to restore an app that you have deleted, you can easily do so using the following command:
cmd package install-existing <packagename>
Final thoughts
Third-party bloatware is almost always an unnecessary annoyance that negatively impacts the performance of your system. It is not usually an active security risk, although, as the “Lenovo incident” discussed in this article shows, this cannot be taken for granted. It is almost always worth uninstalling this kind of software as soon as you unbox your new gizmo.
Software developed by device manufacturers may be somewhat useful, but is rarely essential, and is often inferior to both the apps bundled with the base OS, and with proper commercial third-party options. Unless you really like it, this kind of app is probably also worth removing.
The apps bundled by your OS developer also use up storage space and system resources, and there is a good chance you may never use many of them. Whether they are worth the effort of removing, however, depends on how much such things matter to you. Security, at least, is not a concern here.





