These days, virtual private networks (VPNs) are most commonly associated with commercial consumer-facing VPN services, such as Proton VPN, that allow individuals to bypass censorship,…

Introducing Proton VPN for Business
August 21st, 2023 in For businessToday, we’re happy to announce the official launch of Proton VPN for Business. Since 2016, Proton has been progressively bringing our privacy and security services…

What is Tor Browser?
August 18th, 2023 in For businessTor Browser is a privacy-focused browser that lets you navigate the internet without anyone monitoring your activity or identifying you. It relies on the Tor…
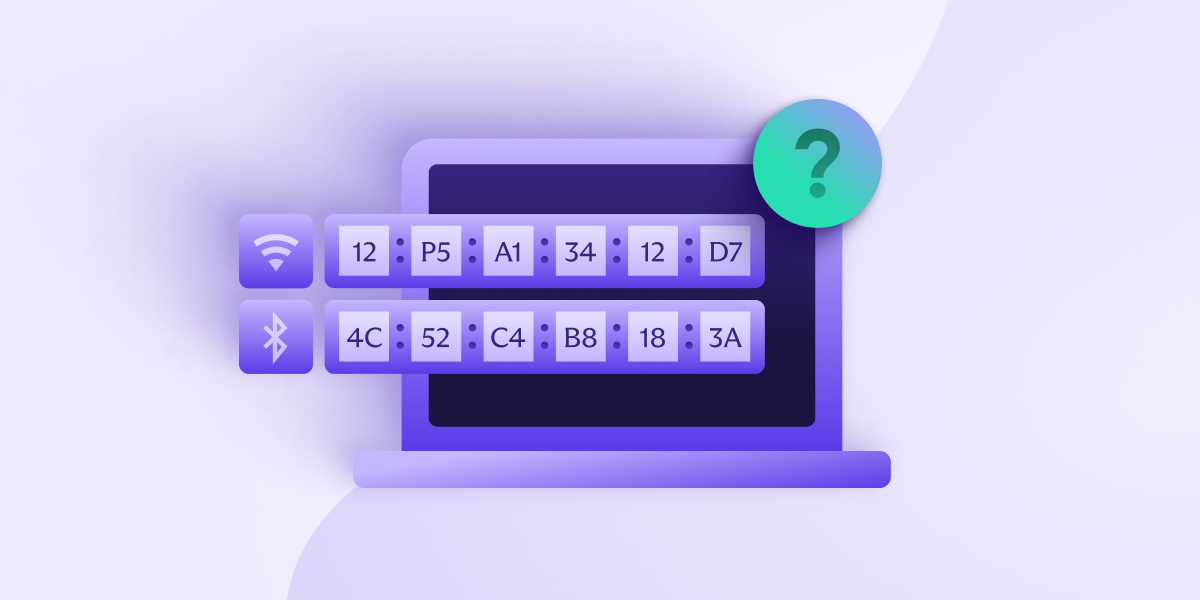
What is a MAC address, and what can it reveal about you?
August 17th, 2023 in For businessEvery device that connects to a network does so through a network interface controller (NIC). Devices that can connect to multiple networks will have a…

Proton VPN Reviews
August 16th, 2023 in For businessWe’ve compiled a full list of recent reviews of Proton VPN’s paid VPN plans. All of these reviews are from independent review sites. This post…

8 common types of cyberattacks and how to prevent them
July 28th, 2023 in For businessHackers are always looking for ways to break through the security systems that defend your devices and data from criminals. From web browsers to operating…

What is I2P and how does it work?
June 30th, 2023 in For businessThe Invisible Internet Project (I2P) is an open-source, decentralized anonymizing network built on similar principles to Tor. Unlike Tor, which was primarily designed to allow…

What is F-Droid and should you use it?
June 23rd, 2023 in For businessF-Droid is an app store for Android that features only free and open-source software (FOSS). This makes it a welcome alternative to the privacy-invading Google…

What are cookies and how are they used?
June 15th, 2023 in For businessInternet cookies, often called website cookies, computer cookies, or just cookies, are small text files that websites store on your computer or device when you…
