IKEv2 is a VPN protocol used to secure VPN connections. Part of the IPSec protocol suite(새 창), it is sometimes (and strictly speaking, more correctly) referred to as IKEv2/IPSec.
A VPN protocol is a set of instructions or rules that determine how the connection between your device and the VPN server is made.
Learn more about how a VPN works
The protocol determines how secure and fast a connection is. OpenVPN and WireGuard® are alternative VPN protocols that we now use exclusively on official Proton VPN apps (plus Stealth, which is based on WireGuard). However, you can still set up Proton VPN using IKEv2 on third-party VPN clients.
IKEv2 is the VPN protocol officially supported on all Apple devices (Mac computers, iPhones, and iPads), but the way that Apple implements VPN connections is badly flawed.
What is IPSec?
Internet Protocol Security (IPSec) is a flexible protocol suite that provides a framework for securing VPN connections. Crucially, it:
- Sets up the key exchange between your device and the VPN server.
- Provides authentication to verify the source of data packets and ensure they haven’t been tampered with during transit.
- Encrypts and decrypts data sent over the VPN connection
As a framework rather than a complete solution itself, IPSec supports multiple protocols and encryption standards to perform these functions.
What is IKEv2?
IKEv2 is the second iteration of the Internet Key Exchange (IKE) protocol. Originally developed by Microsoft and Cisco as part of the IPSec suite, there are now many open-source versions of the protocol.
IKE is used to set up a security association(새 창) (SA) for IPSec when connecting your device and the VPN server. That is, it’s responsible for negotiating a set of mutually agreed-upon keys and algorithms to be used by both parties.
IKE is built on the Oakley protocol(새 창) and Internet Security Association and Key Management Protocol(새 창) (ISAKMP). It uses X.509 certificates(새 창) for authentication and a Diffie-Hellman exchange(새 창) (DHE) to secure the key exchange.
When IPSec is used with IKEv1, it’s often referred to simply as IPSec. IKEv2 was released in 2005 and improves on IKEv1 in several key ways, including using less bandwidth and being able to detect if a connection is still active. If it isn’t, IKEv2 can quickly re-establish a dropped connection.
Another improvement is its support for the Mobility and Multihoming (MOBIKE) protocol, which allows IKEv2 to switch networks easily. For example, when moving between hotspots or between home WiFi and mobile connections.
IKEv2 is also more resistant to denial of service(새 창) (DoS) attacks than IKEv1, is more efficient in terms of the number of cryptographic mechanisms it uses, and can easily traverse through NAT firewalls(새 창).
Is IKEv2/IPSec secure?
The consensus among cryptographic experts is that IKEv2/IPSec is a secure VPN protocol.
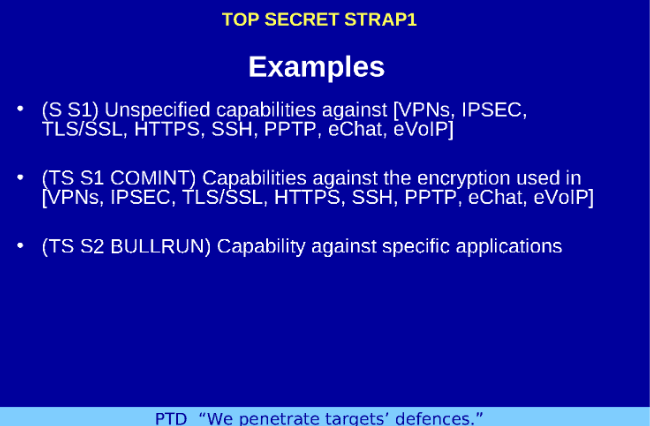
In 2013, John Gilmore(새 창), a technology specialist and founding member of the Electronic Frontier Foundation, published a white paper outlining how IPSec was deliberately weakened(새 창) during its design phase. Additionally, revelations obtained by Edward Snowden(새 창) about the US National Security Agency(새 창) (NSA)’s Bullrun program(새 창) cast further doubt on the security of IPSec.
However, IPSec has no known weaknesses when implemented with IKEv2 (Apple’s implementation of IKEv2 is problematic, but the problem lies with Apple, not IKEv2/IPSec itself).
Final thoughts — IKEv2 vs. OpenVPN and WireGuard
Although IKEv2 is considered secure, OpenVPN is considered even more secure and can be run over TCP for increased censorship resistance. WireGuard is considered to be as secure as OpenVPN, but is also much faster. Under Proton VPN’s implementation, it can also run over TCP.
So while there is nothing wrong with IKEv2, there is also little reason to use it over OpenVPN or (especially) WireGuard these days.
IKEv2 continues to be widely supported because it’s the VPN protocol officially supported on Apple devices. But as we’ve already mentioned, Apple’s implementation of IKEv2 is best avoided.







