Tor is een krachtige privacytool, maar u wilt Tor misschien niet helemaal alleen gebruiken. Leer waarom u misschien verbinding wilt maken met Tor via een VPN.
Wanneer u verbinding maakt met het internet, vooral als u openbare wifi gebruikt, is de kans groot dat mensen u in de gaten houden. Hackers, overheidsspionnen en de websites die u bezoekt, kunnen uw IP-adres, uw locatie, de pagina’s die u bezoekt en zelfs de informatie die u over het netwerk verstuurt en ontvangt, achterhalen. Maar er zijn twee eenvoudig te gebruiken technologieën die u kunnen beschermen: Tor en VPN.
Dit artikel legt uit wat Tor is en waarom u zou kunnen overwegen om Tor via VPN te gebruiken in plaats van Tor op zichzelf.
Wat is Tor en hoe werkt het?
Tor is een gratis softwareprogramma ontwikkeld door The Tor Project(nieuw venster), een non-profitorganisatie gevestigd in Massachusetts. Tor stelt gebruikers in staat hun internetverkeer te anonimiseren, waardoor het een nuttig hulpmiddel is voor journalisten en mensenrechtenverdedigers die online het doelwit kunnen zijn. Tegenwoordig gebruiken veel mensen Tor elke dag, van slachtoffers van huiselijk geweld(nieuw venster) tot prominente klokkenluiders en activisten. Edward Snowden gebruikte een combinatie van Tor en PGP(nieuw venster) om geheime informatie over de NSA met The Guardian te communiceren.
Met Tor kunt u ook verbinding maken met verborgen diensten die bekendstaan als onion-sites, die alleen toegankelijk zijn via het Tor-netwerk. Proton Mail heeft bijvoorbeeld zijn eigen onion-site(nieuw venster). Deze kunnen nuttig zijn voor het omzeilen van regionale censuur(nieuw venster).
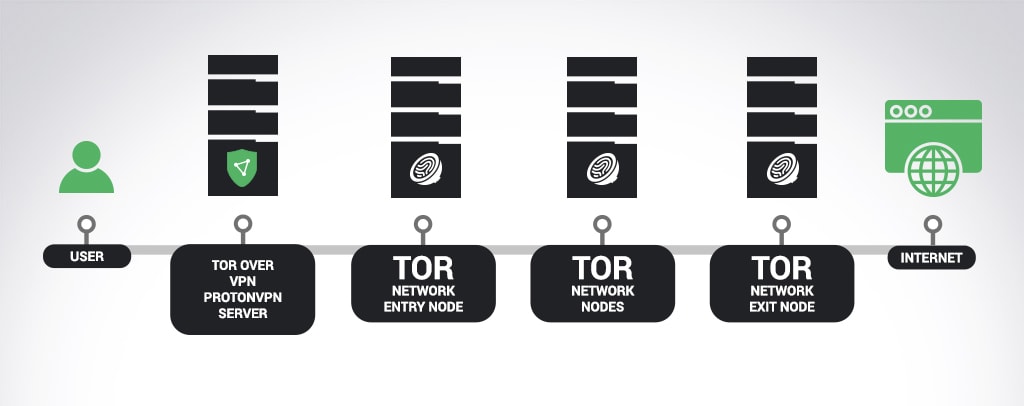
Wanneer u verbinding maakt met het Tor-anonimiteitsnetwerk, wordt uw internetverbinding versleuteld en via meerdere Tor-servers die door vrijwilligers over de hele wereld worden beheerd, doorgegeven. Tenzij het hele Tor-netwerk (of een aanzienlijk deel ervan) wordt gemonitord, kan een derde partij het echte IP-adres van de Tor-gebruiker niet identificeren. Websites die u bezoekt, zien alleen het IP-adres van de Tor-exitnode (de laatste node in het Tor-netwerk waar uw verkeer doorheen gaat), en niet uw werkelijke IP.
Tor gebruiken in combinatie met een VPN
Een VPN, of virtueel privénetwerk, brengt een versleutelde tunnel tot stand tussen uw apparaat en de VPN-server, waardoor uw ware IP-adres en uw activiteiten worden verborgen voor uw internetprovider (ISP) en eventuele hackers of spionnen die het netwerk mogelijk monitoren. (Volg deze links om meer te leren over hoe VPN’s werken en de voordelen van het gebruik ervan.)
Er zijn een paar voordelen aan het gebruik van Tor in combinatie met VPN. Het gebruik van Tor met een VPN geeft u een extra laag privacy omdat de VPN-versleuteling voorkomt dat de Tor-invoernode (de Tor-server waar u het verborgen netwerk betreedt) uw IP-adres ziet. Een gecompromitteerde Tor-invoernode is een veelvoorkomende manier voor een aanvaller om te proberen de anonimiteit van Tor te doorbreken. De VPN versleutelt bepaald internetverkeer dat Tor niet ondersteunt, zoals ICMP-verkeer. Het voorkomt ook dat uw ISP weet dat u verbinding maakt met Tor.
Bovendien geeft het gebruik van Tor via VPN u toegang tot onion-sites zoals die beheerd door Proton Mail(nieuw venster), Facebook(nieuw venster) en The New York Times(nieuw venster), naast vele anderen(nieuw venster).
Er zijn echter ook nadelen aan het gebruik van Tor via VPN. Hoewel Proton VPN zowel TCP- als UDP-verkeer ondersteunt, ondersteunt Tor alleen TCP. (Voor instructies over hoe u Proton VPN configureert om TCP te gebruiken, klik hier.) U moet ook een VPN-dienst gebruiken die u vertrouwt, omdat de VPN-server uw werkelijke IP-adres kan zien. VPN-vertrouwen betekent het gebruik van een gerenommeerde VPN-dienst die geen logs van uw activiteit bijhoudt en geen advertenties of malware serveert. Het is ook belangrijk om te weten waartegen een VPN wel en niet kan beschermen. Proton VPN is de enige VPN-dienst die deze informatie biedt in een uitgebreid overzicht van ons bedreigingsmodel.
Proton VPN en Tor
Er zijn een aantal manieren om Tor te gebruiken. U kunt bijvoorbeeld de Tor-browser(nieuw venster) downloaden, een Tor-plugin gebruiken of een Tor-besturingssysteem(nieuw venster) op uw machine draaien. Proton VPN biedt een eenvoudigere manier om verbinding te maken met het Tor-netwerk als gemak voor betaalde gebruikers. Met een enkele klik krijgt u toegang tot onion-sites en tot de privacyvoordelen van het Tor-netwerk.
Bij Proton VPN implementeren we Tor via VPN, wat betekent dat uw internetverkeer helemaal door het Tor-netwerk is versleuteld en uw ware IP-adres nooit wordt onthuld aan uw ISP of aan Tor-nodes.
Om te beginnen met het gebruik van Proton VPN, klikt u op de inschrijfknop hieronder (het is gratis). Of als u al een gratis account hebt, overweeg dan te upgraden om te profiteren van onze geavanceerde beveiligingsfuncties. Wanneer u klaar bent om verbinding te maken met Tor via Proton VPN, vindt u stapsgewijze instructies hier.
Inschrijven UpgradenU kunt ons volgen op sociale media om op de hoogte te blijven van de laatste Proton VPN-releases:
Twitter(nieuw venster) | Facebook(nieuw venster) | Reddit(nieuw venster)
Neem een gratis Proton Mail versleuteld e-mailaccount(nieuw venster)



