Las revelaciones de Snowden(nueva ventana) revelaron que la NSA está llevando a cabo vigilancia electrónica a escala global y develaron las redes oscuras de las agencias de inteligencia que actúan como cómplices.
Cuando la gente piensa en la vigilancia masiva, con razón piensan en la NSA, pero casi todos los países del mundo tienen su propia agencia de inteligencia de señales (SIGINT). Desde el GCHQ del Reino Unido hasta el BND de Alemania, estas organizaciones se centran en la recopilación de inteligencia, las operaciones de contrainteligencia y la aplicación de la ley mediante la interceptación de comunicaciones y otras señales electrónicas. SIGINT cubre una amplia gama de actividades, desde intervenir teléfonos hasta acceder a la base de datos de correos electrónicos de un usuario con XKEYSCORE(nueva ventana).
Por lo general, una de las pocas restricciones legales establecidas sobre estas agencias es que no pueden espiar a sus propios ciudadanos. Esto crea un fuerte incentivo para que cooperen e intercambien información entre sí. Los Five Eyes, Nine Eyes y Fourteen Eyes son los acuerdos más grandes e importantes que crean el marco legal para tal recopilación de inteligencia coordinada a través de las fronteras.
Además de los acuerdos de Five, Nine y Fourteen Eyes, también existen acuerdos similares de intercambio de inteligencia no occidentales. Esto significa que hay pocos lugares en el mundo donde sus datos personales estén a salvo de espionaje, por lo que debe tomar medidas adicionales, como un cifrado fuerte, para mantenerlos lejos de miradas indiscretas.
La siguiente tabla muestra los países que participan en los acuerdos de intercambio de inteligencia Five Eyes, Nine Eyes y Fourteen Eyes. Para obtener más información sobre cada uno de estos acuerdos, vaya a:
| País | Five Eyes | Nine Eyes | Fourteen Eyes | Otros |
| Reino Unido | ✓ | ✓ | ✓ | |
| Estados Unidos | ✓ | ✓ | ✓ | |
| Australia | ✓ | ✓ | ✓ | |
| Canadá | ✓ | ✓ | ✓ | |
| Nueva Zelanda | ✓ | ✓ | ✓ | |
| Dinamarca | ✓ | ✓ | ||
| Países Bajos | ✓ | ✓ | ||
| Francia | ✓ | ✓ | ||
| Noruega | ✓ | ✓ | ||
| Alemania | ✓ | |||
| Bélgica | ✓ | |||
| España | ✓ | |||
| Suecia | ✓ | |||
| Italia | ✓ | |||
| Israel | ✓ | |||
| Japón | ✓ | |||
| Singapur | ✓ | |||
| Corea del Sur | ✓ |
¿Cómo obtienen estos gobiernos sus datos privados?
Todas las agencias SIGINT confían en las empresas de telecomunicaciones y los proveedores de servicio de internet(nueva ventana) para obtener acceso a los datos privados de las personas. Al instalar divisores de fibra óptica en los puntos de unión del PSI, la agencia SIGINT puede hacer una copia exacta de los datos que se procesan en ese punto. Estos datos luego se analizan mediante inspección profunda de paquetes y se almacenan en diferentes centros de datos.
Acuerdo de intercambio de inteligencia Five Eyes
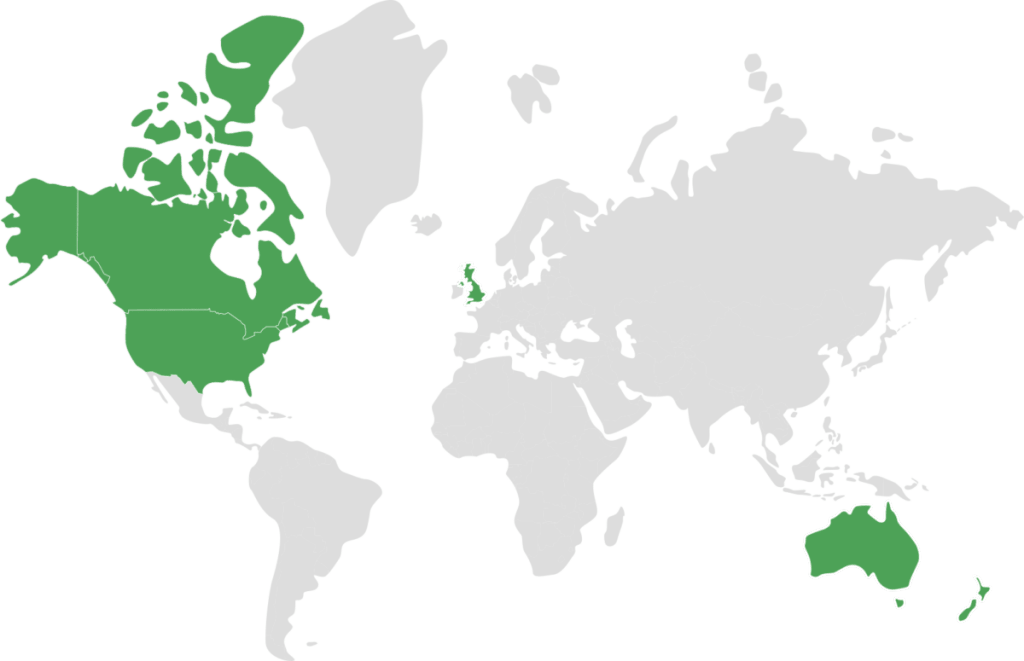
Five Eyes(nueva ventana) (también 5 Eyes o FVEY) es el nombre de la alianza multilateral de intercambio de inteligencia creada por el Acuerdo UKUSA(nueva ventana). El acuerdo fue concebido originalmente como un pacto posterior a la Segunda Guerra Mundial entre el Reino Unido y los EE. UU. en 1946 para espiar a gobiernos extranjeros, específicamente a la URSS. A lo largo de los años, el tratado creció tanto en miembros como en alcance. A medida que internet y la cantidad de datos disponibles para interceptar crecían exponencialmente, el acuerdo comenzó a centrarse más en la vigilancia doméstica.
Los “cinco” en los Five Eyes se refieren a los cinco países anglófonos que observan el tratado:
- Australia
- Canadá
- Nueva Zelanda
- El Reino Unido
- Los EE. UU.
El tratado se ha basado en sus raíces de la Guerra Fría para convertirse en la base de ECHELON(nueva ventana), una serie de estaciones de espionaje electrónico en todo el mundo que pueden interceptar datos transmitidos a través de teléfonos, faxes y computadoras. Esencialmente, las estaciones ECHELON pueden interceptar datos de transmisiones hacia y desde relés satelitales.
Cómo funciona el acuerdo Five Eyes
La alianza Five Eyes es la base de una extensa red de asociaciones entre agencias SIGINT en naciones occidentales para compartir inteligencia entre sí. En casi todos los aspectos, la NSA es el líder mundial en SIGINT, por lo que la mayoría de los acuerdos SIGINT, ya sean multilaterales (como los Five Eyes) o bilaterales, se centran en quién tiene acceso a los datos y la tecnología de la NSA.
Los firmantes del Acuerdo UKUSA se conocen como “segundas partes”, y tienen la mayor cantidad de acceso a los datos de la NSA y los lazos más estrechos con la agencia. Otras naciones occidentales, como los miembros de la OTAN o Corea del Sur, son “terceras partes”. Estos acuerdos de terceros son arreglos formales y bilaterales entre la NSA y la agencia nacional SIGINT. Las terceras partes aún pueden intercambiar datos sin procesar con la NSA, pero tienen menos acceso a su base de datos.
Técnicamente, los ciudadanos de las segundas partes generalmente están exentos de ser espiados sin la aprobación del país anfitrión, pero las revelaciones de Snowden(nueva ventana) han demostrado que la NSA ha creado un marco que podría eludir estos bloques. No ha habido comentarios oficiales de ningún miembro de Five Eyes, y no está claro si estos países han llevado a cabo una vigilancia no aprobada en el pasado. No existe tal restricción para las terceras partes(nueva ventana).
Es importante tener en cuenta que la membresía de estos diferentes grupos cambia constantemente(nueva ventana) en respuesta a los desarrollos globales y políticos. Además, el conocimiento que tenemos de estos grupos ha provenido principalmente de filtraciones, lo que lleva a una imagen difusa y señala cuán poca supervisión tienen estas agencias de inteligencia, que tienen acceso a cantidades casi infinitas de datos personales.
Países del acuerdo Fourteen Eyes

Fourteen Eyes (o 14 Eyes) se refiere al grupo de inteligencia que consta de los países miembros de Five Eyes más:
- Bélgica
- Dinamarca
- Francia
- Alemania
- Italia
- Países Bajos
- Noruega
- España
- Suecia
Estos países participan en el intercambio SIGINT como terceras partes. El nombre oficial de los Fourteen Eyes es SIGINT Seniors of Europe (SSEUR), que ha existido de una forma u otra desde 1982. Similar al Acuerdo UKUSA, su misión original era descubrir información sobre la URSS.
A una reunión de SIGINT Seniors asisten los jefes de las agencias SIGINT (NSA, GCHQ, BND, la DGSE francesa, etc.) y es donde pueden compartir inteligencia y discutir problemas relacionados. Si bien este grupo tiene muchos de los mismos miembros que los “Nine Eyes”, es un grupo diferente. Según documentos filtrados, los Fourteen Eyes no son un tratado formal, sino más bien un acuerdo realizado entre agencias SIGINT.
Alianza de inteligencia Nine Eyes

Nine Eyes(nueva ventana) (9 Eyes) se refiere a un grupo de naciones que comparten inteligencia, compuesto por los países miembros de Five Eyes más:
- Dinamarca
- Francia
- Países Bajos
- Noruega
Estos países participan como terceras partes. Este grupo parece ser un club más exclusivo de SSEUR y no está respaldado por ningún tratado conocido. Al igual que los Fourteen Eyes, es simplemente un arreglo entre agencias SIGINT.
Otros socios
Se sospecha que Israel(nueva ventana), Japón(nueva ventana), Singapur y Corea del Sur(nueva ventana) también son terceras partes con la NSA. Así como hay un SIGINT Seniors of Europe, también hay un SIGINT Seniors of the Pacific(nueva ventana), que se formó en 2005. Sus miembros incluyen a los países miembros de Five Eyes, así como a:
- Francia
- India
- Singapur
- Corea del Sur
- Tailandia
También existen alianzas de intercambio de inteligencia no occidentales, como la Organización de Cooperación de Shanghái(nueva ventana) entre:
- China
- India
- Kazajistán
- Kirguistán
- Pakistán
- Rusia
- Tayikistán
- Uzbekistán
Lo que esto significa para usted
La existencia de acuerdos internacionales de vigilancia como los Fourteen Eyes permite a los países miembros aprovechar, como dice la Electronic Frontier Foundation, “el mínimo denominador común de privacidad(nueva ventana)“. Otros miembros de los Five Eyes se benefician de los datos de vigilancia masiva que aporta el proyecto XKEYSCORE de la NSA. Con el tiempo, los países de los Five Eyes también se beneficiarán de todos los datos que recopila la Ley de Poderes de Investigación del Reino Unido.
Si se aprueba una ley radical que expande la vigilancia electrónica en cualquiera de estos países, es como si la ley se hubiera aprobado en todos los países. También significa que hay una buena posibilidad de que su actividad digital esté siendo capturada y compartida con la NSA u otras agencias SIGINT, sin importar en qué parte del mundo se encuentre.
Cómo evitar la vigilancia
La mejor protección contra esta vigilancia generalizada es un cifrado fuerte. Si cifra sus datos antes de que ingresen a la red, hace que sea mucho más difícil que sea objetivo de vigilancia.
Proteger sus correos electrónicos
Cuando utiliza su cuenta de Proton Mail (nueva ventana)para enviar un correo electrónico a otra persona con una cuenta de Proton Mail, sus correos electrónicos están protegidos con cifrado de extremo a extremo(nueva ventana), lo que significa que nadie puede descifrar el contenido de su mensaje excepto usted y su destinatario. También puede proteger los mensajes que envía a personas que usan diferentes proveedores de correo electrónico con cifrado de extremo a extremo con nuestra función Cifrar para afuera(nueva ventana). Con el cifrado de extremo a extremo y la seguridad adecuada del dispositivo, es más difícil para cualquier agencia SIGINT interceptar, descifrar y leer el contenido de su correo electrónico.
Además, todos los mensajes en los servidores de Proton Mail se almacenan con cifrado de acceso cero(nueva ventana), lo que significa que no podemos compartir el contenido de sus mensajes con agencias de vigilancia. El cifrado de acceso cero significa que ciframos sus mensajes de tal manera que, aunque estén almacenados en nuestros servidores, no podemos acceder a ellos. Otros proveedores de correo electrónico pueden descifrar sus mensajes sin su permiso o conocimiento, ya que controlan las claves que usan para cifrar sus mensajes en su servidor. Al usar cifrado de extremo a extremo y de acceso cero, no podemos proporcionar el contenido de los correos electrónicos de nuestros usuarios a nadie, ni siquiera a gobiernos u organismos encargados de hacer cumplir la ley.
Usar una VPN
Usar un servicio VPN como ProtonVPN(nueva ventana) también hace que sea mucho más difícil para las agencias de vigilancia registrar y rastrear su actividad en internet. Una VPN cifra su tráfico de internet, lo que significa que su PSI no puede registrar su actividad en línea, lo que evita que las agencias SIGINT obtengan esos datos de los puntos de unión del PSI mencionados anteriormente.
Al usar una VPN con Perfect Forward Secrecy (PFS)(nueva ventana), como Proton VPN, también se beneficia de una seguridad adicional. Al usar una clave diferente para cada sesión, PFS significa que incluso si alguna de las claves utilizadas para cifrar una sesión de navegación se ve comprometida, todas sus otras sesiones permanecen seguras. Así que incluso en el improbable evento de que una agencia SIGINT pudiera descifrar los datos VPN de una sesión de navegación, no podrían descifrarlos todos.
Otras aplicaciones
También existen aplicaciones cifradas similares como Wire(nueva ventana) o Signal(nueva ventana) para comunicaciones de chat, y hay algunos navegadores web respetuosos con la privacidad(nueva ventana), como Brave y Firefox, que van más allá en la protección de su privacidad en línea.
Por qué Proton tiene su sede en Suiza
Proton Mail y Proton VPN se basan en Suiza, que tiene algunas de las leyes de privacidad más estrictas del mundo y no es signataria(nueva ventana) de ningún acuerdo de vigilancia. Esto proporciona una capa adicional de protección legal además del cifrado que utilizamos.
Las empresas suizas, como Proton, no pueden ser obligadas a cooperar con solicitudes de datos de usuarios de otros gobiernos. Si el gobierno de otro país quisiera los pocos datos que tenemos sobre cualquiera de nuestros usuarios, tendrían que hacer una solicitud a las autoridades suizas correspondientes, que tienen requisitos estrictos y generalmente no trabajarán con gobiernos que tienen malos registros en derechos humanos. En el caso de que se nos presente una solicitud legal de datos de usuario con la que debemos cumplir, no podemos entregar el contenido de los correos electrónicos ya que nuestro cifrado de acceso cero significa que no tenemos acceso a ellos. La escala de las operaciones de vigilancia masiva es realmente impresionante y una amenaza importante para la sociedad democrática. Es por eso que, en Proton, no confiamos en ningún gobierno para proteger la privacidad de quienes usan Proton Mail o Proton VPN. En cambio, confiamos en la fuerza matemática de nuestros métodos de cifrado de código abierto. Afortunadamente, ahora existen herramientas para proteger su privacidad y salvaguardar su derecho a la libertad en línea.
Preguntas frecuentes
Cifrar sus datos es la mejor manera de protegerse contra la vigilancia masiva. Al usar una VPN(nueva ventana), evita que su PSI recopile datos sobre su actividad en línea (y cualquier agencia gubernamental que esté copiando esos datos). Si su PSI no tiene información sobre lo que hace en línea, no puede compartirla con las agencias SIGINT en los países de Five Eyes.
Sin embargo, si usa una VPN con sede en un país de Five Eyes, cualquier registro que guarden sobre su actividad en línea se puede compartir con todas las agencias SIGINT en el acuerdo UKUSA. Proton VPN tiene su sede en Suiza(nueva ventana), que no forma parte de los acuerdos de Five, Nine o Fourteen Eyes.
Lo mismo puede decirse del cifrado de sus correos electrónicos. Al cifrar sus correos electrónicos, se asegura de que nadie más pueda acceder al contenido de sus mensajes. (Nota: Si envía un correo electrónico a alguien que no está utilizando un servicio de correo electrónico cifrado, el contenido de sus correos electrónicos no estará protegido por cifrado de acceso cero de su lado).
También puede usar navegadores centrados en la privacidad(nueva ventana) y mensajería cifrada(nueva ventana) para protegerse aún más de la vigilancia masiva.
Los Five Eyes (a veces escrito como 5 Eyes o FVEY) es una referencia a los cinco países anglófonos que son miembros del acuerdo UKUSA: Australia, Canadá, Nueva Zelanda, el Reino Unido y los Estados Unidos. Aunque se le perdonaría por pensar que “Eyes” se refiere al espionaje, el término “Five Eyes” en realidad se usó originalmente como abreviatura de “AUS/CAN/NZ/UK/US EYES ONLY”(nueva ventana) en documentos secretos. A medida que se formaron más alianzas de inteligencia — los Nine Eyes y Fourteen Eyes — adoptaron la misma convención de nombres, aunque no hay evidencia de que se usaran como abreviatura de la misma manera.
SIGINT es la forma corta de inteligencia de señales y se refiere a la interceptación de señales de transmisión. Esto generalmente toma la forma de recopilar inteligencia de comunicaciones entre personas (a veces llamada COMINT), aunque también puede incluir inteligencia electrónica (ELINT), que utiliza sensores electrónicos (como radar) para recopilar información.
SIGINT se usó originalmente en la guerra y no afectó a los ciudadanos comunes. Sin embargo, desde la Guerra Fría, las agencias SIGINT han comenzado a recopilar cada vez más inteligencia de las comunicaciones de la gente común. Esto aumentó dramáticamente después de la invención de la World Wide Web, ya que los gobiernos pudieron obtener más datos que nunca sobre personas de todo el mundo, como mostraron las revelaciones de Snowden(nueva ventana).
El acuerdo UKUSA (entonces llamado BRUSA) fue firmado por el Reino Unido y los EE. UU. en 1946. En la década siguiente, las “segundas partes” — Australia, Canadá y Nueva Zelanda — también se convirtieron en signatarios del Acuerdo.





