Every device that connects to a network does so through a network interface controller(yeni pencere) (NIC). Devices that can connect to multiple networks will have a separate NIC for each connection they support. For example, a laptop that supports WiFi, Ethernet (wired), and Bluetooth connections would have three NICs (each with its own MAC address).
Every NIC is identified by a unique media access control (MAC) address, a 12-digit hexadecimal(yeni pencere) number assigned to it by the NIC’s manufacturer (for example, e0:6c:4f:8b:aa:d7).
- What is a MAC address used for?
- Do MAC addresses change?
- What can a Mac address reveal about you?
- Other vulnerabilities
- How to find your MAC address
- How to hide your MAC address
- Does a VPN protect your MAC address?
What is a MAC address used for?
A MAC address identifies the hardware connected to a network. This is typically a local area network (LAN), such as those found in most modern homes and offices, where devices are connected via WiFi or Ethernet cables to a shared router. Devices that connect to each other using Bluetooth form another type of network that uses MAC addresses.
When a device connects to a network, it sends the NIC’s MAC address to the router or Bluetooth receiver, which then assigns it an IP address.
Since each network interface on a network has a unique and unchanging MAC address, MAC addresses are very useful for identifying and diagnosing network issues. For example, they can provide a network administrator with a much more reliable way to identify where data packets are sent or received than dynamic IP addresses, which can change at any time.
Another common use of MAC addresses is for MAC address filtering. This is a security measure that restricts access to a network based on connecting devices’ MAC addresses. If a device without an authorized MAC address attempts to connect to a network, the connection will be refused.
A company, for example, might use MAC filtering to ensure that only employees’ verified laptops can join the office’s local area network (LAN).
MAC addresses can also be used to track down and identify stolen devices.
Do MAC addresses change?
No. Unlike IP addresses, which can routinely change, MAC addresses are hard coded(yeni pencere) into NICs by their manufacturer and never change.
However, it is possible to deliberately “spoof” a device’s MAC address(es), which hides its real MAC address and displays a different address to networks that the device attempts to connect to. We discuss MAC spoofing in greater depth below.
What can a MAC address reveal about you?
NIC manufacturers often identify their chips using a special number sequence called the organizationally unique identifier(yeni pencere) (OUI). This makes up the first six hexadecimal digits of the MAC address. You can see a list of OUIs from well-known NIC manufacturers here(yeni pencere).
Although not a major concern, knowing your device manufacturer could potentially provide hackers with clues to manufacturer vulnerabilities that they can exploit.
MAC addresses and tracking
A MAC address uniquely identifies your device to each new network it connects to. MAC addresses can therefore be used to track your location as you move between WiFi networks and Bluetooth receivers(yeni pencere).
Most MAC address tracking is performed by retailers(yeni pencere) to deliver effective targeted advertising, but it can also be used for government surveillance.
For example, documents released by NSA whistleblower Edward Snowden(yeni pencere) show that the Canadian spying agency CSEC(yeni pencere) illegally used MAC addresses collected from passengers who connected to the free internet service at a major Canadian airport to track the wireless devices of thousands of ordinary airline passengers(yeni pencere) for days after they left the terminal.
It should be stressed, however, that MAC addresses can only identify devices on a local network they are connected to, or within WiFi or Bluetooth detection range. They can’t be forwarded through the network gateway (for example a router), and so MAC addresses can’t be used to track you by someone on the internet.
Other vulnerabilities
MAC addresses are more of a privacy risk than a security risk. MAC flooding(yeni pencere) is an attack that targets network switches and can compromise the security of networks, but is a minimal threat to individual devices or their users.
Networks that rely solely on MAC filtering to provide security are also vulnerable to being compromised by an attacker who spoofs the MAC address of an authorized user. But again, this affects networks, not your device.
How to find your MAC address
On most computers, it’s easy to find the MAC address of all available network adapters (NICs). For this guide, we’ll concentrate on identifying the MAC address of the WiFi or LAN NICs, but it’s also easy to find the MAC addresses of Bluetooth adapters.
Windows
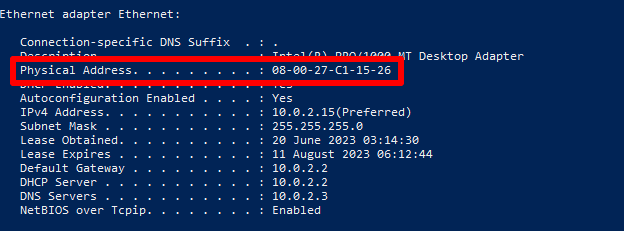
Open the Windows PowerShell or Command Prompt (cmd) app and enter ipconfig /all. Under your WiFi or Ethernet interface, look for the Physical Address.
macOS
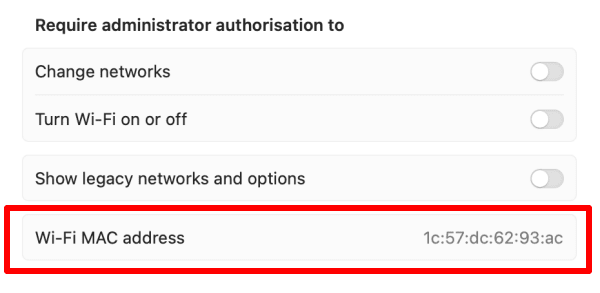
To find the MAC address of your Mac’s WiFi, go to Settings → Wi-Fi → Advanced → Wi-Fi MAC address.
If your Mac has an Ethernet connection, you can find its MAC address by going to Settings → Network → Other Services → your LAN connection → Details → Hardware → Mac address.
Linux
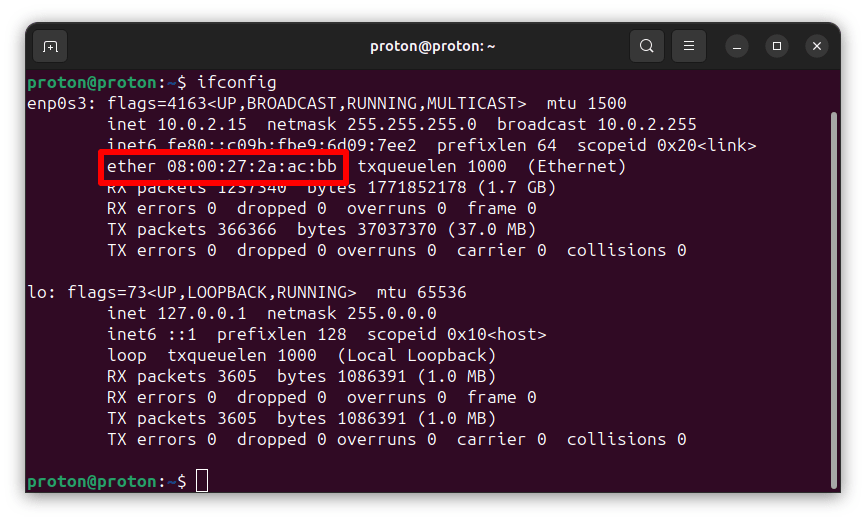
Open a terminal window and enter ifconfig. Under your WiFi or Ethernet interface, look for ether followed by your hexadecimal MAC address.
Android
This guide uses a Samsung One UI device: details may vary depending on your Android version.
Go to Settings → About phone → Status information. Here, you can see your real WiFi MAC address, Bluetooth MAC address, and Ethernet MAC address (if available).
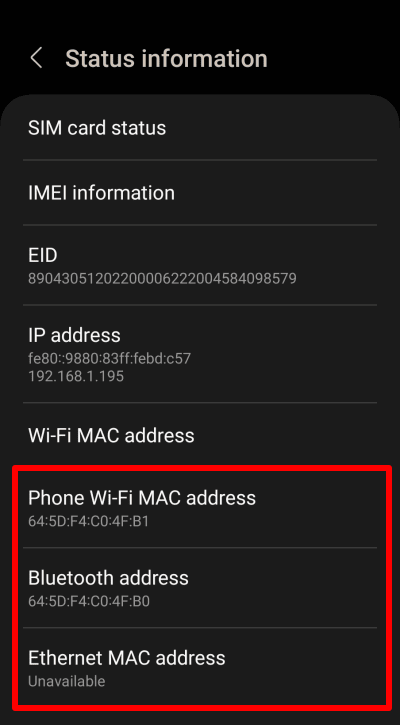
Note that the MAC address used on your WiFi network differs from your device’s real WiFi MAC address. We’ll discuss this below.
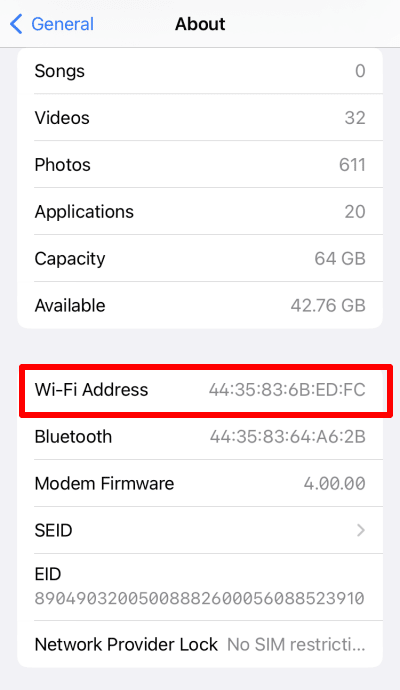
iOS and iPadOS
Go to Settings → General → About →Wi-Fi Address (you can also see your iPhone or iPad’s Bluetooth MAC address here).
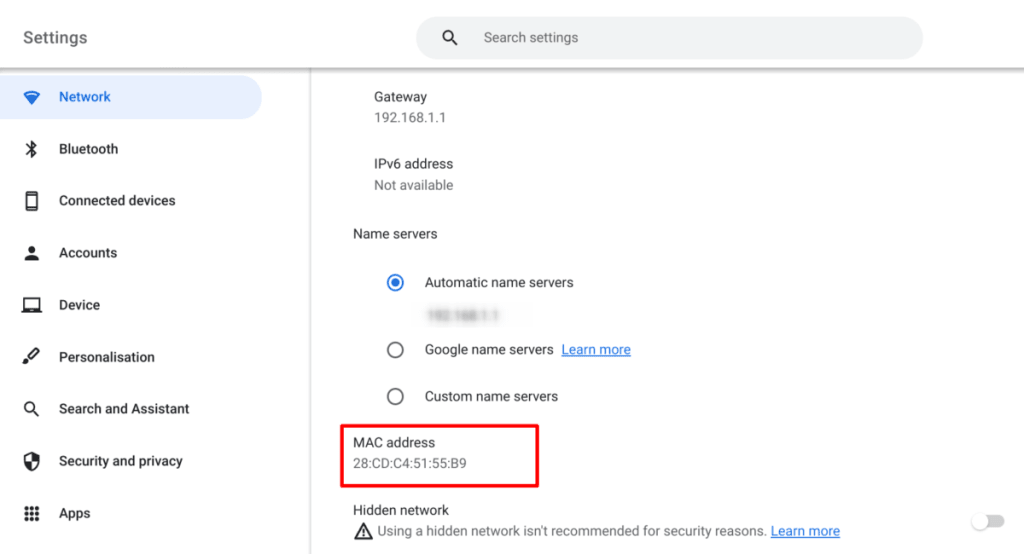
Chromebook
Go to Settings → Network → Wi-Fi → your WiFi network → MAC address.
How to hide your MAC address
As discussed above, retailers and governments can use your MAC address to track your movements. To defend against this, you can “spoof” your MAC address. Note that spoofing your MAC address doesn’t remove the “real” MAC address hard coded into your NIC but hides it and broadcasts an alternative MAC address instead.
Most major operating systems can now help protect your privacy by broadcasting randomized MAC addresses when searching for new WiFi connections. To help avoid networking issues and avoid problems on networks that use MAC address filtering, most desktop platforms will use your real MAC address when you actually make a connection.
Although Apple supports MAC address randomization on all modern iPhones, iPads, and iWatches, this feature is not available on macOS.
Windows
MAC address randomization on Windows 10 and 11 is turned off by default and may not work on all WiFi adapters (especially older ones). To enable it on Windows 11, go to Settings → Network & Internet → WiFi → toggle the Random hardware addresses switch on.
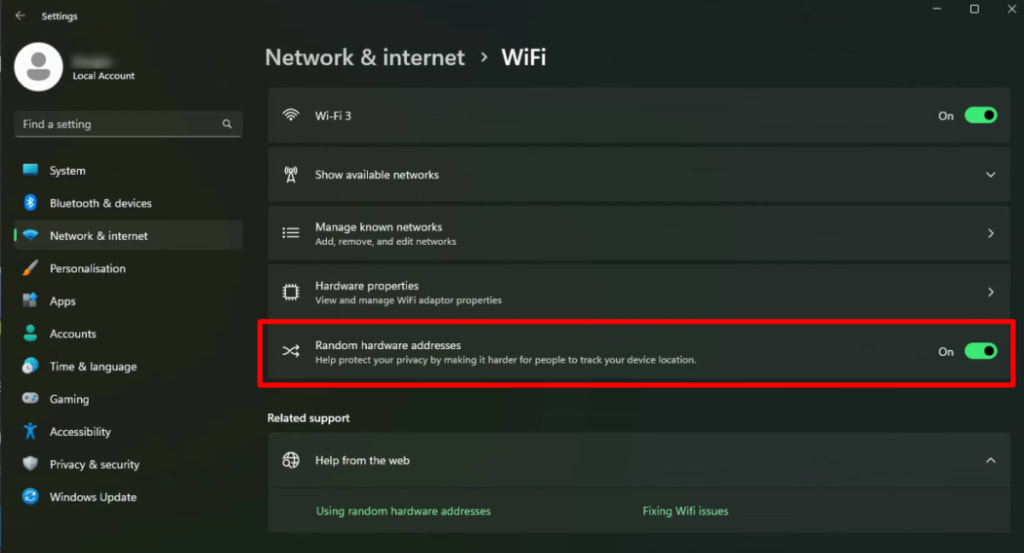
To enable MAC address randomization on Windows 10, go to Settings → Network & Internet → Wi-Fi → Advanced options → toggle the Random hardware addresses switch on.
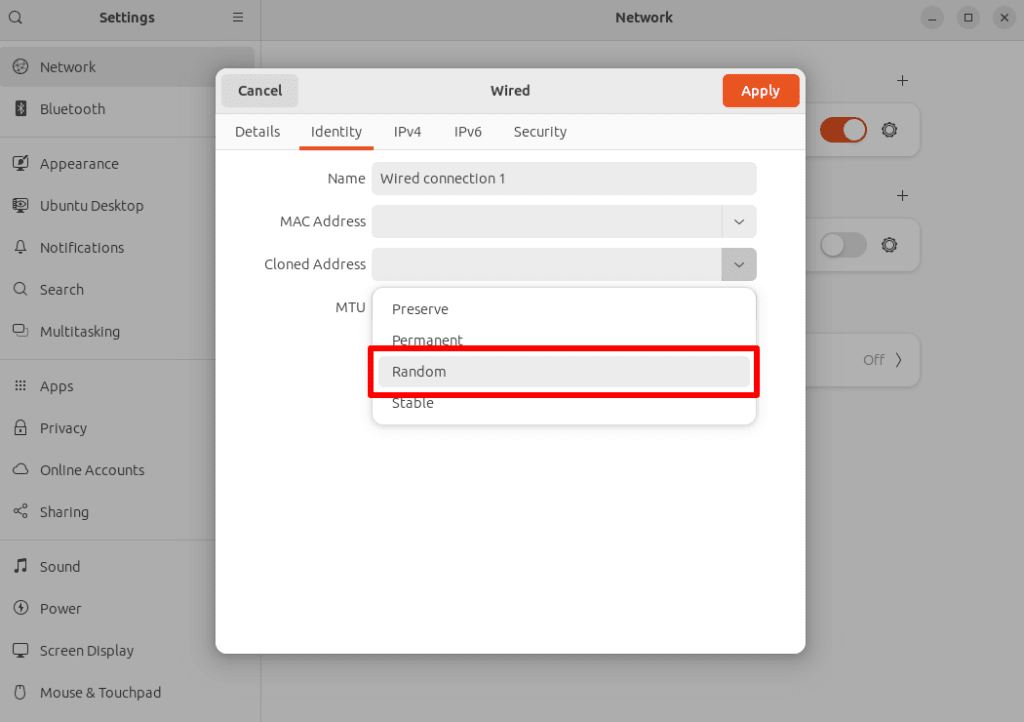
Linux
Support for MAC address randomization on Linux varies primarily by the desktop environment (DE) you use (rather than the distribution). However, it is supported by many DEs. For example:
On GNOME (the default desktop environment for Ubuntu, Fedora, and many other popular distros), go to Settings → Network, click the gear icon next to your connection → Identity → Cloned Address → and select Random from the dropdown menu.
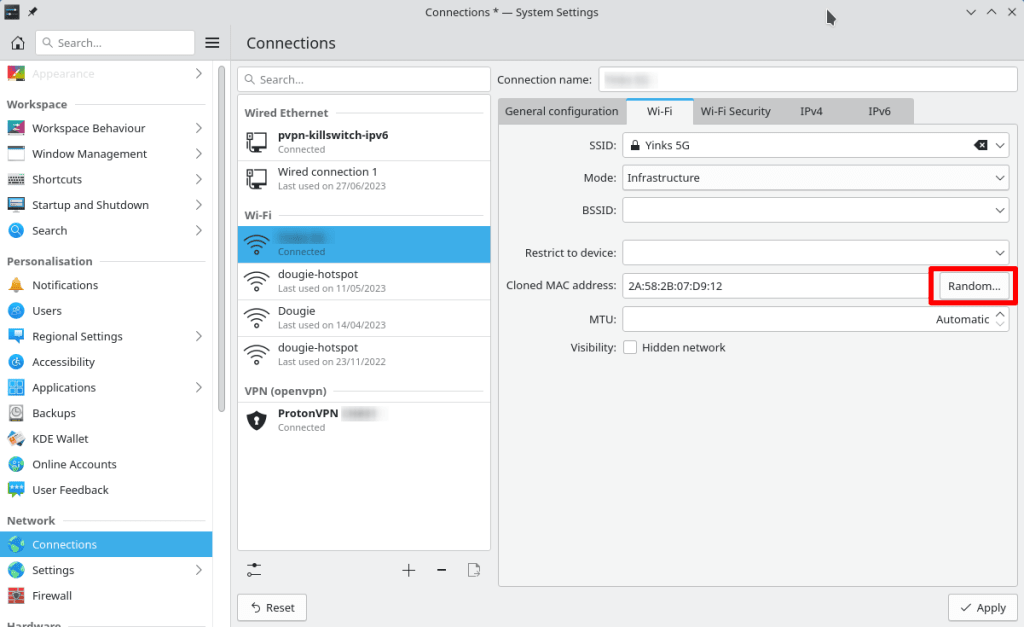
On KDE Plasma o KDE Neon, go to System Settings → Network → Connections → select your connection → Wi-Fi → Cloned MAC address and click the Random button,
Android
Android has supported MAC address randomization since Android 8, but with Android 10, it turbocharged the concept. Instead of just using MAC address randomization when scanning for new networks, Android 10+ devices issue a new random MAC address for each WiFi network that you connect to.
This feature is enabled by default. To change it:
1. Go to Settings → About phone → Status information → WiFi MAC address → select your Current network or any Saved networks → View more. Here you can see the MAC address used for just this network.
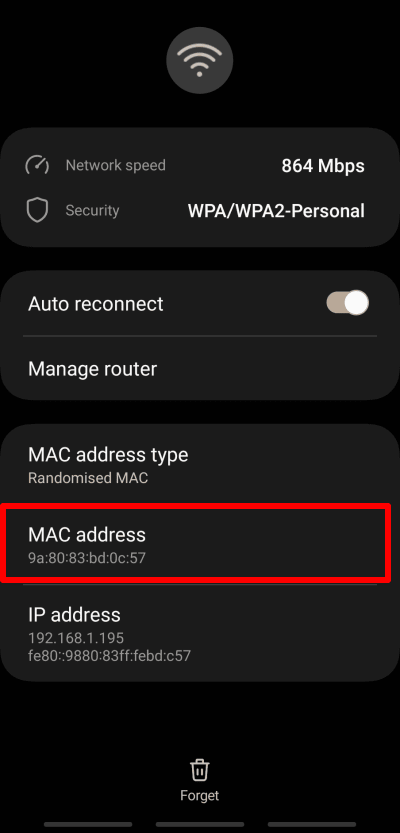
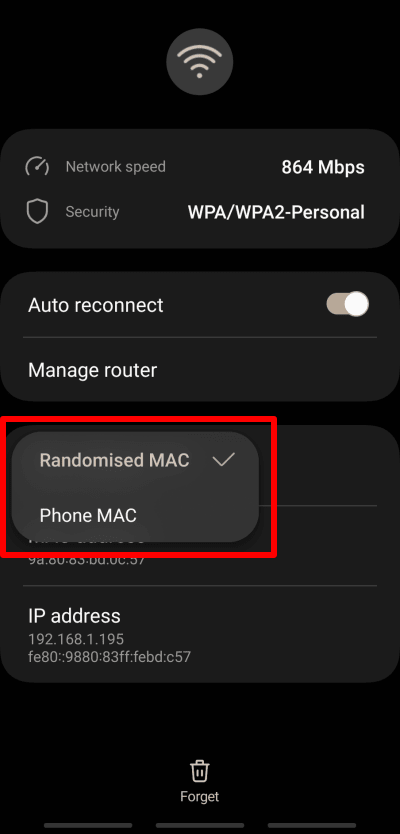
2. Tap MAC address type and choose between Randomised MAC and Phone MAC.
iOS and iPadOS
Apple only introduced MAC address randomization with iOS 14 and iPadOS 14, but Apple products apply it not just when scanning networks, but also for each new network that you join (similar to Android).
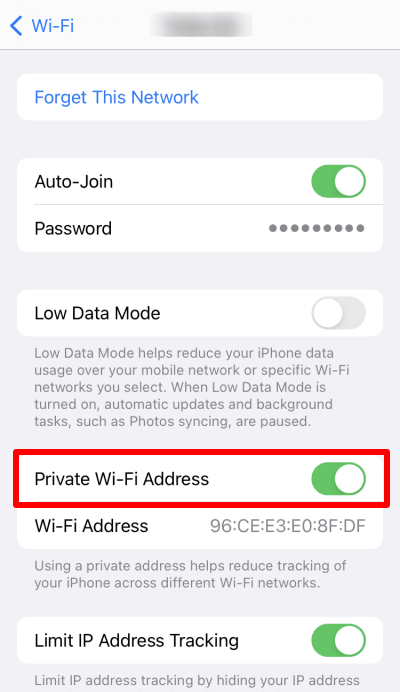
MAC address randomization is enabled by default on iOS and iPadOS 14+ devices. To disable (or enable) the feature, go to Settings → Wi-Fi → your WiFi network → and toggle the Private WiFi Address switch off (or on).
Chromebook
Chrome OS automatically uses MAC address randomization, which can’t be disabled. However, it’s only used for network detection, so your real MAC address is used when you actually connect to a network.
Does a VPN protect your MAC address?
No. A VPN protects your real IP address, but does nothing to hide your MAC address. By hiding your IP address with a VPN (such as Proton VPN), you prevent your internet service provider (and by extension, your government) from seeing what you do online and websites from uniquely identifying you by your IP address.
Learn more about how a VPN protects your privacy
Final thoughts
MAC addresses play an essential role in connecting your device to any network (including the internet). Knowing your MAC address offers limited help to a malicious hacker who wants to access your device, but it can occasionally cause headaches for network administrators.
MAC addresses can present a potentially serious privacy risk, as third parties can use them to track you as you move between (local) networks. However, most modern operating systems have introduced some form of MAC address randomization designed to counter this threat.








